Technology
Winter storms can knock out your tech fast: Prepare now

States prepare for massive winter storm
FOX Weather meteorologist Bayne Froney joins ‘America’s Newsroom’ in Dallas, Texas as the first signs of a massive winter storm begin to show. Texas is preparing accordingly following the devastating winter storm five years ago.
NEWYou can now listen to Fox News articles!
Weather forecasters are warning that a major winter storm is expected to impact large portions of the United States starting Friday. Forecasts call for snow, freezing rain and ice stretching from Texas and the Southern Plains through the Southeast, Mid-Atlantic and into the Northeast. This system is concerning because it combines ice accumulation, gusty winds and plunging temperatures. In many regions, especially across the South and parts of the Mid-Atlantic, infrastructure is not designed to handle prolonged ice events.
That increases the risk of extended power outages and disrupted cell service. When the grid goes down, everyday tech becomes critical. Phones, alerts, vehicles and apps may be your only connection to updates and emergency help. Preparing now matters far more than reacting later.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM newsletter.
RUSSIAN WINTER STRIKE LEAVES NEARLY 800K HOMES WITHOUT POWER AND HEAT IN UKRAINE’S DNIPRO REGION
Ice storms can take down power lines fast, leaving homes without electricity and cell service for hours or even days. (AP Photo/Charles Krupa)
Why ice storms are especially disruptive
Ice storms cause more damage than most people expect. Unlike snow, ice sticks to everything and adds significant weight. Ice builds up on trees and power lines, causing branches to snap and lines to fall. Utility crews often cannot begin repairs until conditions improve, which delays restoration. Forecasters at Fox Weather warn that freezing rain across the South and interior Southeast could be particularly damaging, while snow and wind farther north may slow emergency response.
Even if cell towers remain standing, networks often overload during severe weather. When thousands of people try to call at once, connections fail. Texts and alerts usually have a better chance of getting through. That is why you should assume you may be offline longer than expected.
Immediate tech actions to take before the storm hits
These steps are simple, but timing matters. Do them before the weather conditions worsen.
Charge devices and prepare backup power
- Charge all phones, laptops, tablets and battery packs
- Fully charge wearable devices like smartwatches
- Turn on Low Power Mode on phones now
- Lower screen brightness to extend battery life, and check out these other tips to keep your phone battery charged longer
- Make sure you have a reliable portable charger on hand, like those highlighted in our 5 best portable chargers for emergencies on Cyberguy.com
- For outages that could last days in this winter storm, a good generator can keep your home powered the longest and safest
- Reliable lighting matters during storms and blackouts. Invest in a high-output flashlight and hats with built-in lights that can be especially useful when visibility is poor
- Keep a battery-powered weather radio on hand so you can receive emergency updates even if power and cell service go out
A fully charged phone, smart power settings and a reliable portable charger can keep you connected early in an outage while longer-term home power solutions carry you through the days ahead.
A woman walks with an umbrella in the rain in the Manhattan borough of New York, Feb. 5, 2014. (REUTERS/Carlo Allegri)
Plan for offline communication and limited cell service
- Download offline maps for your area.
- Save emergency contacts locally on your device.
- Write down key phone numbers on paper.
- Plan to text instead of calling if networks are congested. Text messages use less bandwidth and often go through when calls fail.
- Cold weather can also make phones harder to use. Touchscreen-compatible winter gloves let you stay connected without exposing your hands to the cold.
Set up a family check-in plan before the storm
- Agree on specific check-in times
- Choose one out-of-area contact everyone can message
- Avoid constant calling, which can overload networks
Clear expectations reduce panic and unnecessary phone use
Make sure emergency alerts are enabled
Emergency alerts can reach your phone even when apps and social media cannot. They are designed to cut through network congestion and deliver critical warnings.
How to turn on emergency alerts on iPhone
- Open Settings
- Tap Notifications
- Scroll to Government Alerts
- Turn on Emergency Alerts
- Enable Always Play Sound
- Turn on Imminent Threat Alerts under Enhanced Safety Alerts
US POWER CRUNCH LOOMS AS OKLO CEO SAYS GRID CAN’T KEEP UP WITHOUT NEW INVESTMENT
Ice storms add heavy weight to trees and power lines, causing widespread damage and outages that can overwhelm repair crews and communication networks for longer than expected. (AP/Craig Ruttle)
How to turn on emergency alerts on Android
Settings may vary, depending on your Android phone’s manufacturer
- Open Settings
- Tap Safety and emergency or Notifications
- Select Wireless emergency alerts
- Turn on Severe threats and Extreme threats
- Enable Allow alerts and Alert sound
On some phones, you may also see options for Public safety messages or Emergency alerts, which should be turned on. These alerts may include evacuation notices, shelter updates and severe weather warnings.
Both iPhone and Android let you preview alert sounds and settings in these menus, so take a moment to test them now and make sure alerts are loud enough before severe weather hits.
Know how to use Emergency SOS on your phone
If you need help during a winter storm, Emergency SOS can contact emergency services even when you cannot unlock your phone or make a normal call. Set this up now. Do not wait until you are stressed, cold or without power.
How to set up and use Emergency SOS on iPhone
- Open Settings
- Tap Emergency SOS
- Turn on Call with Hold and Release or Call with 5 Button Presses
- Scroll down and add emergency contacts
To activate Emergency SOS during an emergency, press and hold the side button and a volume button, or quickly press the side button five times, depending on your settings.
How to set up and use Emergency SOS on Android
Settings may vary, depending on your Android phone’s manufacturer
- Open Settings
- Tap Safety and emergency or Privacy and safety
- Select Emergency SOS
- Turn on Use Emergency SOS
- Choose how SOS is triggered, such as Require to swipe to call
- Add emergency contacts and medical information by clicking Emergency sharing settings
On many Android phones, pressing the power button five times will trigger Emergency SOS. Emergency SOS can call for help, share your location and alert emergency contacts when conditions are dangerous.
If cell towers go down during this storm, features like Emergency SOS can still help you reach emergency services. Our guide explains in more detail how these lifesaving settings work.
Apps you should have installed ahead of time
The right apps can deliver critical updates when power is out, cell networks are strained and social media is unreliable. Install and set these up before the storm arrives.
Weather and severe alert apps
- Fox Weather app: A trusted option for real-time forecasts, winter storm alerts, radar tracking and location-based notifications. Make sure local alerts are turned on.
- MyRadar Weather Radar: A highly rated radar app that shows storm movement in real time and sends push alerts when severe weather is approaching your area.
- Storm Shield Severe Weather App: Delivers National Weather Service alerts based on your exact location, similar to NOAA weather radio warnings, with clear push notifications for winter storms and ice events.
- NOAA Weather Radio apps (iPhone and Android): These apps stream official NOAA Weather Radio broadcasts, providing continuous updates, watches and warnings directly from the National Weather Service. Weather radio streams often remain available even during major outages.
Using more than one weather app can give you redundancy if one service is delayed or overloaded.
Utility and outage tracking apps
- Your local power utility app: Most utilities offer apps that allow you to report outages, view outage maps and track restoration progress in real time.
- FEMA App: Provides official weather alerts, disaster resources, shelter locations and safety guidance during severe weather events.
These apps can confirm outages, provide restoration updates and reduce unnecessary calls to utilities when systems are overwhelmed.
Do not overlook vehicle tech and preparedness
Your vehicle may become a critical resource during extended outages.
Prep your car before conditions worsen
- Fill your gas tank early. A full tank allows you to run the engine briefly for heat or charging if needed.
- Keep a phone charger in the car.
- Store a fully charged portable power bank in the glove box or center console. This gives you emergency phone power if your car battery dies or you cannot run the engine.
- Download weather and road condition alerts.
- Also, consider buying a Snow brush and ice scraper, jumper cables, a set of 6 LED Road Flares Emergency Lights and a First Aid Trauma Pack with QuikCloth, so you will not be caught off guard in an emergency.
- There are also portable tech solutions designed to help you stay warm and powered during outages or roadside delays, including heated gear worth purchasing in advance.
Storms also bring scams and fraud attempts
Severe weather creates ideal conditions for scams. Power outages, delayed responses and anxiety make people more likely to trust messages that appear urgent or official.
Fake utility and restoration scams
Scammers often impersonate electric, gas or water utilities.
- Texts or calls claiming your power will be restored sooner if you pay
- Messages warning service will be shut off unless you act immediately
- Spoofed phone numbers that look like your local utility
What to know: Utilities do not charge fees to restore power and do not demand payment by text, gift cards or apps.
Emergency aid and disaster relief scams
These scams spike right after storms hit.
- Messages promising emergency funds, fuel vouchers or hotel assistance
- Fake charity links claiming to help storm victims
- Social media posts asking for donations using stolen images
What to know: Legitimate aid is announced through official government or well-known nonprofit channels, not unsolicited messages.
Fake delivery, fuel and repair service scams
Storms disrupt normal services, which scammers exploit.
- Links claiming fuel delivery is available in your area
- Messages about delayed packages that require confirmation
- Ads for emergency home repairs that ask for upfront payment
What to know: Do not click links or pay deposits without verifying the company independently.
Charging your devices and lining up backup power now can make the difference between staying informed during an outage and being cut off once the storm hits. (Kurt “CyberGuy” Knutsson)
Account takeover and identity theft attempts
Storm chaos makes it easier for attackers to slip through unnoticed.
- Password reset emails pretending to be from banks or retailers
- Login alerts asking you to “secure” your account immediately
- Calls claiming suspicious activity that push you to share codes
What to know: Never share one-time codes or login details, even if the message looks legitimate.
How to protect yourself before and during the storm
Taking a few precautions now can help you avoid costly mistakes when outages, delays and scam messages start piling up.
1) Slow down and verify every urgent message
Scammers rely on panic. If a message pressures you to act fast, stop and verify it through a trusted source.
2) Avoid clicking links in unsolicited messages and use strong antivirus software
Go directly to official websites or apps instead of tapping links in texts or emails. Keep your operating system up to date, and use strong antivirus software to block malicious links and fake websites.
The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
Get my picks for the best 2026 antivirus protection winners for your Windows, Mac, Android and iOS devices at Cyberguy.com.
3) Lock down accounts before outages hit
Enable two-factor authentication (2FA) on email, banking, and utility accounts so stolen passwords cannot be used alone.
4) Reduce your exposure with a data removal service
Many storm scams work because criminals already have your phone number, address or email. Using a data removal service to opt out of data broker sites can reduce how easily scammers target you during emergencies.
While no service can guarantee the complete removal of your data from the internet, a data removal service is really a smart choice. They aren’t cheap, and neither is your privacy. These services do all the work for you by actively monitoring and systematically erasing your personal information from hundreds of websites. It’s what gives me peace of mind and has proven to be the most effective way to erase your personal data from the internet. By limiting the information available, you reduce the risk of scammers cross-referencing data from breaches with information they might find on the dark web, making it harder for them to target you.
Check out my top picks for data removal services, and get a free scan to find out if your personal information is already out on the web by visiting Cyberguy.com.
Get a free scan to find out if your personal information is already out on the web: Cyberguy.com.
5) Never pay to restore power or receive aid
Utilities and government agencies do not charge fees to restore service or release emergency assistance.
When power and internet access are limited, it is harder to verify messages quickly. That makes preparation just as important as awareness. A little skepticism now can prevent financial loss and identity theft when help is hardest to reach.
Take my quiz: How safe is your online security?
Think your devices and data are truly protected? Take this quick quiz to see where your digital habits stand. From passwords to Wi-Fi settings, you’ll get a personalized breakdown of what you’re doing right and what needs improvement. Take my Quiz here: Cyberguy.com.
Kurt’s key takeaways
Winter storms can turn small tech decisions into critical ones. Ice, power outages and overloaded cell networks can leave people cut off faster than expected, especially in regions not built for prolonged winter weather. Preparing your devices, alerts, vehicles and accounts ahead of time gives you more control when conditions worsen. It also reduces panic and limits your exposure to scams that thrive during emergencies. A little planning now can make a big difference when help is harder to reach.
Have you taken steps to prepare your tech for this winter storm, or did this checklist highlight something you still need to do? Let us know by writing to us at Cyberguy.com.
CLICK HERE TO DOWNLOAD THE FOX NEWS APP
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM newsletter.
Copyright 2026 CyberGuy.com. All rights reserved.

Technology
Google’s AI search is so broken it can ‘disregard’ what you’re looking for

Google’s AI Overviews are running into an interesting problem right now. Earlier on Friday, if you searched for the term “disregard,” the AI Overview section would include a response like what you’d see from a more traditional AI chatbot instead of the typical AI summary, as spotted on X. As you can see in the image at the top of this story, I got an AI Overview response that said, “Got it. If you need anything else or have a new question later, just let me know!”
As of Friday afternoon, however, Google isn’t showing an AI Overview for the term “disregard” at all — instead, it shows a list of news stories about the issue first. Google hasn’t replied to our requests for comment. In a statement to Android Authority, a spokesperson said that “We’re aware that AI Overviews are misinterpreting some action-related queries, and we’re working on a fix, which will roll out soon.”
AI Overviews haven’t just been tripping up over the word “disregard.” When searching for “ignore,” Google’s AI Overview section showed the following message to a Verge colleague:
Message received! I’m here and ready to help. What would you like to focus on today? Just let me know if there’s a specific topic, task, or question you’d like to explore.
When they searched “skip,” the AI Overview section said:
It looks like your message was just a test or a typo! Feel free to ask a question, share a prompt, or let me know how I can help you with your tasks today. I’m ready whenever you are!
As of Friday afternoon, Google is still showing me AI Overviews with broken responses when I search for “ignore” and “skip.”
As funny as this all is, it’s almost certainly just some kind of bug — I expect Google will fix it soon enough. Maybe Google Search itself is tired after everything that happened at Google I/O.
Updates, May 22nd: Google now isn’t showing AI Overviews for “disregard.” Also added a Google statement.
Technology
Fox News AI Newsletter: AI girlfriend dumps Hollywood filmmaker

Paul Schrader attends a special screening of “Oh, Canada” at IFC Center in New York City on Dec. 5, 2024. (Dia Dipasupil/Getty Images)
NEWYou can now listen to Fox News articles!
Welcome to Fox News’ Artificial Intelligence newsletter with the latest AI technology advancements.
IN TODAY’S NEWSLETTER:
– Oscar-nominated filmmaker disappointed his AI girlfriend dumped him
– AI layoffs may be backfiring on companies
– Nvidia CEO Jensen Huang warns China has ‘all the chips they need’ despite US bans
BAD BREAK-UP: Dating in the digital era isn’t easy, as one Oscar-nominated filmmaker learned the hard way. Paul Schrader, the screenwriter of Martin Scorsese classics like “Taxi Driver” and “Raging Bull,” revealed in a Facebook post that he had dabbled in developing an “AI girlfriend.”
ROI MIA: A lot of workers have had the same uneasy thought lately: “Is AI coming for my job?” It is a fair question. Companies keep talking about automation, AI agents and lower costs. Some workers hear that and wonder whether their next performance review will come with a chatbot-shaped shadow in the room. However, a new Gartner study suggests the story may be more complicated. Many companies are cutting jobs while adopting AI, but those cuts are not clearly producing better returns.
‘ALL THE CHIPS THEY NEED’: In a stark warning to Washington policymakers, Nvidia CEO Jensen Huang revealed that U.S. technology export bans may be triggering unintended consequences, declaring that China-backed rival Huawei is actively “flourishing in our absence.”
TOUGH CROWD: Former Google CEO Eric Schmidt was met with boos during a University of Arizona commencement speech after discussing artificial intelligence and fears the technology could reshape – or replace – parts of the workforce.
PAINFUL ERROR: Students at Glendale Community College revolted against AI when it was revealed during their graduation ceremony that the robot tasked with announcing the names of the new graduates experienced a glitch and skipped over hundreds of students who were set to hear their names as they walked across the stage.
BATTLE OF THE TITANS: A federal jury ruled against Elon Musk in his lawsuit accusing OpenAI of abandoning its nonprofit roots, finding that neither the tech company nor CEO Sam Altman could be held liable in the matter because Musk waited too long to bring the case.
NEXT-GEN WARFARE: A top U.S. defense contractor pulled back the curtain on AI-powered systems designed to hunt down and destroy swarms of enemy drones as the U.S. rapidly expands its next-generation warfighting capabilities.
‘UNSETTLING’: Standard Chartered CEO Bill Winters on Wednesday walked back comments he made at an investor event Tuesday when he said the bank plans to cut thousands of jobs as it replaces what he called “lower-value human capital” with tech powered by artificial intelligence (AI).
OPINION: There’s a revolution underway in American education, and first lady Melania Trump and the White House are leading the way, Arthur Herman and Beth Herman write.
SLOW DOWN: Waymo is temporarily halting freeway operations for its robotaxi service in several U.S. markets as the company works to address performance issues in construction zones, FOX Business has learned.
‘NOT GOING AWAY’: New York Times staffers got up from their workspaces inside the paper’s New York City headquarters on Wednesday and gathered outside to rally against management, demanding a fair contract and insisting the company puts profits over people. The event, dubbed “Rally for a Fair Contract,” came as the Times Guild is fighting for protections against artificial intelligence, guaranteed hybrid work, affordable health care, pay increases that match the rising cost of living and keeping work within the union.
SWEET MOVE: A Florida community has deployed AI-powered robotic beehives as declining bee populations continue raising concerns about the future of the US food supply.
BLOCKBUSTER DEAL: NextEra Energy is making a massive $66.8 billion bet that America’s artificial intelligence boom will drive a historic surge in electricity demand, announcing plans to acquire Dominion Energy to create the world’s largest regulated utility by market value.
BEAM ME UP: New York City’s LaGuardia Airport is bringing science fiction to the terminal with the debut of an AI-powered hologram concierge designed to help travelers find gates, lounges and baggage claim through face-to-face conversations.
DISAPPEARING ACT: Chatting with AI can feel casual until the question gets personal. Maybe you want to ask about a health concern. Maybe you need help understanding a loan. Or maybe you want career advice without feeling like your question is sitting in a data file somewhere. That is the idea behind Incognito Chat with Meta AI, a new private chat mode Meta says is coming to WhatsApp and the Meta AI app.
APP OVERHAUL: Airbnb is pushing far beyond home rentals, rolling out airport pickups, grocery delivery, luggage storage, car rentals, boutique hotels and exclusive travel experiences as it expands deeper into travel services. The app is also adding boutique and independent hotels in major cities including New York, Paris, London, Rome and Singapore, alongside new AI-powered features like review summaries, listing comparisons and smarter customer support tools.
Subscribe now to get the Fox News Artificial Intelligence Newsletter in your inbox.
FOLLOW FOX NEWS ON SOCIAL MEDIA
YouTube
X
SIGN UP FOR OUR OTHER NEWSLETTERS
Fox News First
Fox News Opinion
Fox News Lifestyle
Fox News Health
DOWNLOAD OUR APPS
Fox News
Fox Business
Fox Weather
Fox Sports
Tubi
WATCH FOX NEWS ONLINE
Fox News Go
STREAM FOX NATION
Fox Nation
Stay up to date on the latest AI technology advancements and learn about the challenges and opportunities AI presents now and for the future with Fox News here.
Technology
Twelve South’s AirFly Pro 2 has hit one of its best prices ahead of summer travel

With Memorial day weekend kicking off the travel season, we’re seeing a lot of deals pop up on travel gadgets, from portable power banks to noise-canceling headphones. One of the best right now is Twelve South’s AirFly Pro 2 Bluetooth adapter, which lets you use your wireless headphones with in-flight entertainment systems so you can enjoy your flight a little more. It’s currently down to $49.99 ($10 off) at Amazon and directly from Twelve South, which is one of its best prices to date.
The Bluetooth transmitter lets you ditch the airline’s wired earbuds in favor of your own Bluetooth headphones or earbuds, which makes for a much better in-flight listening experience. All you need to do is plug the AirFly Pro 2 into the headphone jack on a seatback entertainment system, pair your headphones, and you’re set. It also supports two pairs of headphones at once, so you can watch movies or listen to podcasts with a travel companion.
As Twelve South’s premium AirFly model, the Pro 2 also adds a few welcome improvements that make it even easier to use. That includes the cheaper AirFly SE’s dedicated onboard volume controls as well as an upgraded processor, which enables faster pairing and improved sound quality with less background noise. Its battery should also last up to 25 hours on a single charge, which should comfortably last you through even the longest flights.
The AirFly Pro 2 remains useful long after you land, too. As it works with any standard audio jack, you can also use it to connect your wireless headphones to devices like a Nintendo Switch , older car stereos, and even compatible gym equipment like treadmills.
-
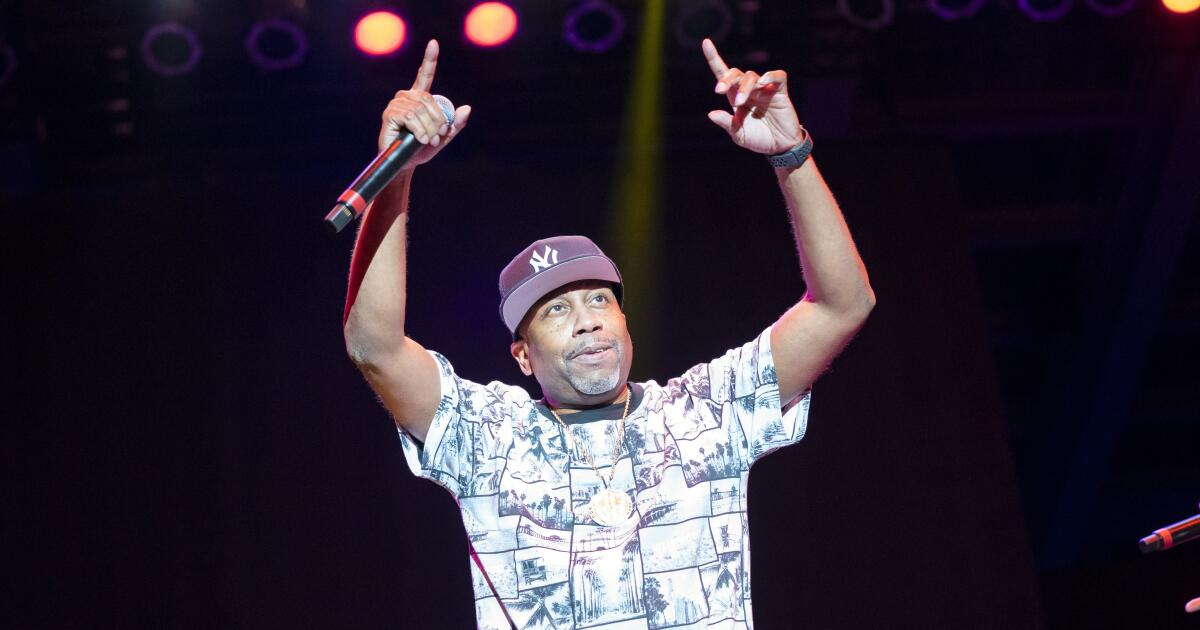
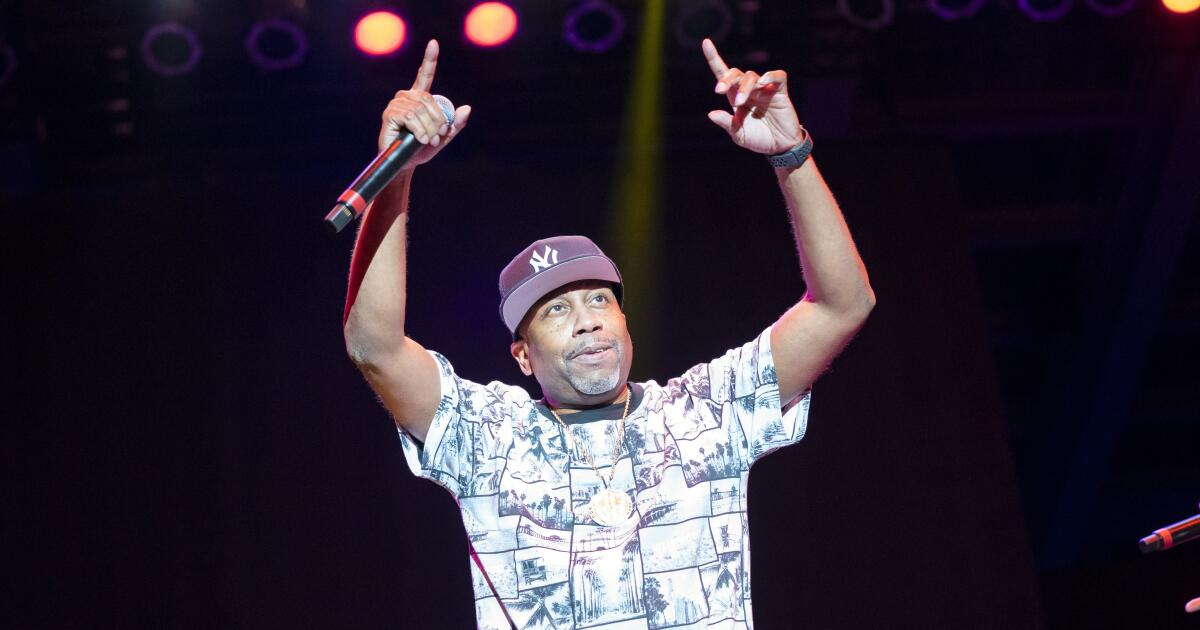 Entertainment2 minutes ago
Entertainment2 minutes agoRob Base, rapper known for ‘It Takes Two,’ dies at 59
-

 Lifestyle8 minutes ago
Lifestyle8 minutes agoAt SoCal newest children’s museum, kids can dig for mammoth bones or face a giant Lite-Brite
-

 Politics14 minutes ago
Politics14 minutes agoGOP governor hopefuls give closing arguments to oft-forgotten Central Valley Republicans
-

 Science20 minutes ago
Science20 minutes agoSome experts say they’ve never seen bees swarm so early — and that’s concerning
-

 Sports26 minutes ago
Sports26 minutes agoPrep talk: Teenage barber is helping baseball players look good during playoffs
-

 World38 minutes ago
World38 minutes ago‘United States of the Middle East?’: Trump posts US flag covering Iran
-

 News1 hour ago
News1 hour agoWhat will Trump do next with Iran?
-

 New York3 hours ago
New York3 hours agoHow Stars From ‘The Morning Show’ and ‘The League’ Keep Their Love Alive









