A trove of leaked documents from a Chinese state-linked hacking group shows that Beijing’s intelligence and military groups are carrying out large-scale, systematic cyber intrusions against foreign governments, companies and infrastructure — exploiting what the hackers claim are vulnerabilities in U.S. software from companies including Microsoft, Apple and Google.
Washington
Leaked files from Chinese firm show vast international hacking effort

The files — posted to GitHub last week and deemed credible by cybersecurity experts, although the source remains unknown — detail contracts to extract foreign data over eight years and describe targets within at least 20 foreign governments and territories, including India, Hong Kong, Thailand, South Korea, the United Kingdom, Taiwan and Malaysia. Indian publication BNN earlier reported on the documents.
“We rarely get such unfettered access to the inner workings of any intelligence operation,” said John Hultquist, chief analyst of Mandiant Intelligence, a cybersecurity firm owned by Google Cloud. “We have every reason to believe this is the authentic data of a contractor supporting global and domestic cyberespionage operations out of China,” he said.
U.S. intelligence officials see China as the greatest long-term threat to American security and have raised alarm about its targeted hacking campaigns.
Experts are poring over the documents, which offer an unusual glimpse inside the intense competition of China’s national security data-gathering industry — where rival outfits jockey for lucrative government contracts by pledging evermore devastating and comprehensive access to sensitive information deemed useful by Chinese police, military and intelligence agencies.
The documents come from iSoon, also known as Auxun, a Chinese firm headquartered in Shanghai that sells third-party hacking and data–gathering services to Chinese government bureaus, security groups and state–owned enterprises.
The trove does not include data extracted from Chinese hacking operations but lists targets and — in many cases — summaries of sample data amounts extracted and details on whether the hackers obtained full or partial control of foreign systems.
One spreadsheet listed 80 overseas targets that iSoon hackers appeared to have successfully breached. The haul included 95.2 gigabytes of immigration data from India and a 3 terabyte collection of call logs from South Korea’s LG U Plus telecom provider. The group also targeted other telecommunications firms in Hong Kong, Kazakhstan, Malaysia, Mongolia, Nepal and Taiwan. The Indian Embassy in Washington did not respond to a request for comment on the documents.
ISoon clients also requested or obtained infrastructure data, according to the leaked documents. The spreadsheet showed that the firm had a sample of 459GB of road–mapping data from Taiwan, the island of 23 million that China claims as its territory.
Road data could prove useful to the Chinese military in the event of an invasion of Taiwan, analysts said. “Understanding the highway terrain and location of bridges and tunnels is essential so you can move armored forces and infantry around the island in an effort to occupy Taiwan,” said Dmitri Alperovitch, a national security expert and chairman of Silverado Policy Accelerator, a think tank.
Among other targets were 10 Thai government agencies, including the country’s foreign ministry, intelligence agency and senate. The spreadsheet notes that iSoon holds sample data extracted from those agencies from between 2020 and 2022. The Thai Embassy in Washington did not respond to a request for comment.
Most of the targets were in Asia, though iSoon received requests for hacks further afield. Chat logs included in the leak describe selling unspecified data related to NATO in 2022. It’s not clear whether the data was collected from publicly available sources or extracted in a hack. NATO did not immediately respond to a request for comment.
Another file shows employees discussing a list of targets in Britain, including its Home and Foreign offices as well Treasury. Also on the list were British think tanks Chatham House and the International Institute for Strategic Studies.
“In the current climate, we, along with many other organizations, are the target of regular attempted attacks from both state and non-state actors,” said a Chatham House spokesperson, who said the group is “naturally concerned” about the leaks but has protection measures in place.
Asked about the leaked documents, the U.K. foreign office declined to comment.
The hackers also facilitated attempts to extract information from close diplomatic partners including Pakistan and Cambodia.
China encourages hacking rivalry
ISoon is part of an ecosystem of contractors that emerged out of a “patriotic” hacking scene established over two decades ago and now works for a range of powerful government entities including the Ministry of Public Security, the Ministry of State Security and the Chinese military.
According to U.S. officials, hackers with the People’s Liberation Army have breached computer systems in about two dozen key American infrastructure entities over the past year in an attempt to establish a foothold and be able to disrupt power and water utilities as well as communications and transportation system.
China’s model of mixing state support with a profit incentive has created a large network of actors competing to exploit vulnerabilities and grow their business. The scale and persistence of their attacks are headaches for American technology giants like X, Microsoft and Apple, which are now locked in a constant race to outsmart the hackers.
All software products have vulnerabilities, and a robust global marketplace rewards those who find back doors or develop tools known as exploits to take advantage of them. Many software vendors offer bounties to reward researchers who report security flaws, but government contractors in the United States and elsewhere often claim these exploits — paying more for the right to use them in espionage or offensive activity.
U.S. defense and intelligence contractors also develop tools for breaking into software, which are then used by federal officials in surveillance and espionage operations, or in offensive cyberweapons.
Chinese security researchers at private companies have demonstrably improved in recent years, winning a greater number of international hacking competitions as well as collecting more bounties from tech companies.
But the iSoon files contain complaints from disgruntled employees over poor pay and workload. Many hackers work for less than $1,000 a month, surprisingly low pay even in China, said Adam Kozy, a former FBI analyst writing a book on Chinese hacking.
The leaks hint at infighting and dissatisfaction in the network of patriotic Chinese hackers, despite the long-standing collaboration between groups.
Although it’s unclear who released the documents and why, cybersecurity experts said it may be an unhappy former employee or even a hack from a rival outfit.
The leaker presented themselves on GitHub as a whistleblower exposing malpractice, poor work conditions and “low quality” products that iSoon is using to “dupe” its government clients. In chats marked as featuring worker complaints, employees grumbled about sexism, long hours and weak sales.
Within China, these groups present themselves as essential to the Communist Party’s extensive campaign to eliminate threats to its rule from cyberspace.
China has in recent years escalated its efforts to trawl international public social media and trace targets abroad, though the crossover between public mass-monitoring and private hacking is often unclear.
ISoon has signed hundreds of deals with Chinese police that range from small jobs priced at $1,400 to multiyear contracts costing as much as $800,000, one spreadsheet showed.
The company’s leaked product manuals describe the services they offer and their prices, and boast about being able to steal data without detection. The product descriptions, targeted at state security clientele, at times use wartime language to describe a data-extraction mission underpinned by extreme threats to China’s national security.
“Information has increasingly become the lifeblood of a country and one of the resources that countries are scrambling to seize. In information warfare, stealing enemy information and destroying enemy information systems have become the key to defeating the enemy,” reads one document describing an iSoon package for sale that, it claims, would allow clients to access and covertly control Microsoft Outlook and Hotmail accounts by bypassing authentication protocols.
ISoon’s product manuals also advertise a $25,000 service for a “remote access” control system to obtain Apple iOS smartphone data from a target, including “basic mobile phone information, GPS positioning, mobile phone contacts” and “environment recording.”
One pitch advertised a service in which iSoon could efficiently conduct phishing campaigns against individuals or groups of Twitter users. Another outlined services that would allow the firm to remotely control targeted Windows and Mac operating systems.
Apple, Microsoft, Google and X, formerly Twitter, did not respond to requests for comment.
In addition to striking long-term agreements, iSoon regularly worked on demand in response to requests from police in smaller Chinese cities and with private companies, according to pages of chat logs between the company’s top executives.
Sometimes the clients knew exactly what they wanted — for example, to find the identity of a specific Twitter user — but they also often made open-ended requests. In one exchange, employees discussed a request from a state security bureau in southern China asking if iSoon had much to offer on nearby Hong Kong. An iSoon employee suggested emails from Malaysia instead.
The scattershot approach appeared motivated in part by pressure from clients to deliver more and higher quality information. But despite the company boasting of cutting-edge capabilities, chats show that clients were regularly unimpressed with the hacked information.
ISoon repeatedly failed to extract data from government agencies, internal discussions showed, with some local authorities complaining about subpar intelligence.
Although some of iSoon’s services focused on domestic threats, the company often highlighted its ability to target overseas targets in the region — including government departments in India and Nepal, as well as in overseas Tibetan organizations — to attract clients. In December 2021, the group claimed that it had gained access to the intranet of the Tibetan Government in Exile, setting off a frantic search for a buyer. Some 37 minutes later, the company had found an interested client.
Another product — priced at $55,600 per package — is meant to allow control and management of discussion on Twitter, including using phishing links to access and take over targeted accounts. ISoon claims the system then allows clients to find and respond to “illegal” and “reactionary sentiments” using accounts that are centrally controlled by the client to “manipulate discussion.”
The documents show that iSoon met and worked with members of APT41, a Chinese hacking group that was charged by the U.S. Justice Department in 2020 for targeting more than 100 video game firms, universities and other victims worldwide.
Afterward, iSoon’s founder and CEO, Wu Haibo, who goes by the alias “shutd0wn,” joked with another executive about going for “41” drinks with Chengdu 404 — the organization APT41 is a part of — to celebrate them now being “verified by the Federal Bureau of Investigation.”
But chat messages between executives from 2022 suggest that relations between the groups had soured because iSoon was late in paying Chengdu 404 more than 1 million yuan ($140,000). Chengdu 404 later sued iSoon in a dispute over a software development contract.
Wu and his team appeared blasé about the idea that they would one day be charged by U.S. authorities like APT41. In July 2022, an executive asked Wu whether the company was being closely watched by the United States. “Not bothered,” Wu replied. “It was a matter of sooner or later anyway.”
Neither iSoon nor Wu responded to emailed requests for comment.
Pei-Lin Wu and Vic Chiang in Taipei and Lyric Li in Seoul contributed to this report.

Washington
Pulitzer-winning Washington Post editor Dan Eggen found dead at 60 after being laid-off earlier this year

Veteran Washington Post editor Dan Eggen — a key architect of the paper’s political coverage who was laid off in a brutal round of cuts earlier this year — was found dead at his home in the nation’s capital on Tuesday. He was 60.
No foul play or violence were suspected in the death, local authorities told Eggen’s family, according to WaPo. The cause of death was pending an autopsy as of Wednesday morning.
Eggen spent nearly three decades at the paper, helping steer its reporting on the White House, Congress and presidential campaigns. He was on a team that won a 2002 Pulitzer Prize for investigating the plotters behind 9/11, going on to work on projects that won the most prestigious award in journalism in 2016, for reporting on Russian election interference, and in 2022, for exploring the previous year’s attack on the US Capitol.
A fixture of the newsroom’s most sensitive coverage, Eggen was “a sharp editor with a keen story sense,” the Post’s executive editor Matt Murray told staff.
“Dan was involved in hiring, editing and mentoring dozens of politics writers across the years,” he wrote, adding that Eggen’s “news muscle and instincts were integral to our coverage.”
At the time of his death, Eggen was set to start a new job at NOTUS, a recently launched, DC-based outlet that’s been scooping up laid-off WaPo staffers.
“We hired Dan to join us at NOTUS after some of the best reporters in DC told us he was the best editor they’d ever had,” the site’s editor in chief Tim Grieve wrote on X. “We were excited to have him here, and I think he was equally excited to be coming here. Deepest condolences to everyone who loved him.”
Josh Dawsey, a Wall Street Journal reporter who previously covered the White House for the Washington Post, recalled Eggen’s relentless work ethic. The late journalist “worked seven days a week, 14 hours a day” and was “incredibly dedicated, a wonderful line editor” who pushed reporters to improve, Dawsey told WaPo.
“I viewed him as one of the true beating hearts of the newsroom … Dan is one of those people who make the newspaper work,” he added.
Ashley Parker, a former White House reporter for the Washington Post who has since decamped to The Atlantic, remembered Eggen as a deeply collaborative editor who empowered his staff, saying he “was the rare editor who believed in his reporters” and “changed only 10 percent of your copy but made it 90 percent better.”
Eggen began his WaPo career as a metro reporter and covered the post-9/11 Justice Department before becoming an editor.
He is survived by two children from his ex-wife, journalist Stephanie Armour, and a sister, according to WaPo.
The Post has sought comment from local police.
Washington
‘Not just workers’: Calls for safer roads during National Work Zone Awareness Week

Incidents like the one in 2023 along the Baltimore Beltway — a crash that killed six highway workers — are the reason why officials gathered to stress the need for better work zone safety during National Work Zone Awareness Week.
This week, officials, workers and residents are calling for safer roads as they say there is still more work to be done when it comes to safety.
“It’s about understanding that each of us has a role to play in the safety and protection of one another,” William Pines from the Maryland State Highway Administration said.
With an active construction site as the backdrop — at the interchange between Pennsylvania Avenue and Suitland Parkway — roadway workers spoke up.
“We are not just workers, we are people — real people. We are parents, siblings, friends and neighbors. So when you see us out there, please pay attention to that.” Dawn Hopkins with Flagger Force Traffic Control Services said.
Hopkins says she’s had to sound an alarm to get her crew out of dangerous situations.
“Please slow down, stay alert…and watch out for us in the workzones,” Hopkins added.
While the number of crashes in Maryland work zones in 2025 remains concerning, it is lower than in 2024. In 2025, there were:
- 1,148 work zone crashes
- 9 work zone deaths
- 449 injuries
In 2024, there were:
- 1,302 work zone crashes,
- 12 work zone deaths, and
- 492 injuries
“While citations are down, we still had 19 citations that were issues where the automated system recorded drivers traveling in excess of 130 miles an hour in work zones,” Pines said.
Maryland Gov. Wes Moore has proclaimed April 22 as “Go Orange Day” in Maryland, urging everyone to wear orange in support of highway worker safety.
A moment of silence for road workers who have been killed will be observed at noon this Friday.
Washington
Q1 market trends in Northern VA and Washington DC | ARLnow.com

This regularly scheduled column is written by Eli Tucker, Arlington-based Realtor and Arlington resident. If you would like to work with Eli and his team in Northern Virginia and the greater D.C. Metro area, you can reach him directly at [email protected].
Question: How has the local real estate market performed so far this year?
Answer: After a year where market conditions softened in favor of buyers, the Northern VA real estate market became more favorable for sellers in the first quarter of 2026, while the Washington DC condo market continued to reel.
What is in this article:
- Northern VA, Arlington, and Washington DC Absorption Trends (demand)
- Northern VA, Arlington, and Washington DC Inventory Trends (supply)
- Washington DC List Price Trends (market values)
Northern VA & Arlington Inventory is Being Absorbed Faster
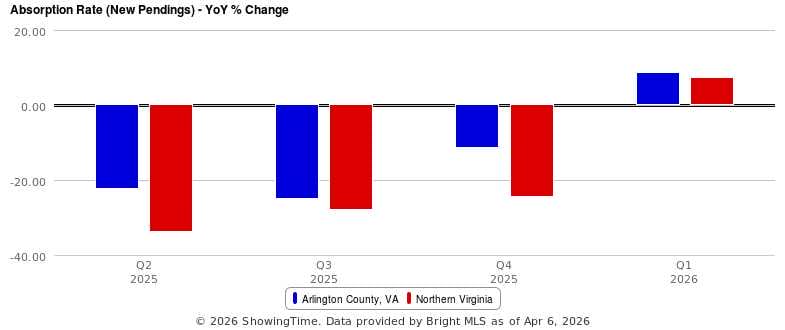
After four straight quarters of double-digit decreases in year-over-year absorption, the Northern VA and Arlington markets saw a ~8% increase in absorption rate.
What this means: Demand increased in Q1
Northern VA & Arlington New Listing Volume is Declining
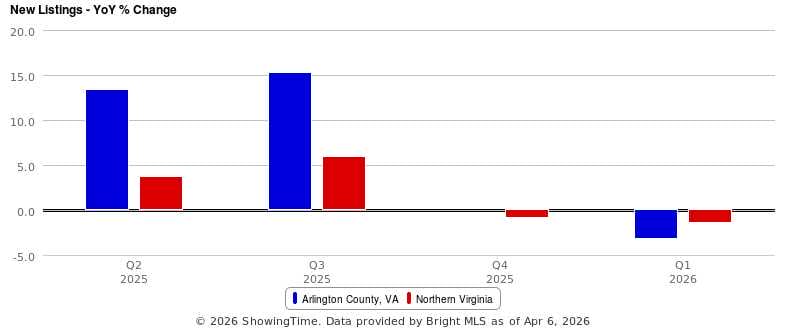
After a promising trend of six straight quarters of year-over-year increases in the number of homes listed for sale in Northern VA, new listing activity fell by ~1% each of the previous two quarters.
What this means: Sellers have less competition, buyers have fewer choices
Washington DC Condo Absorption is Plummeting
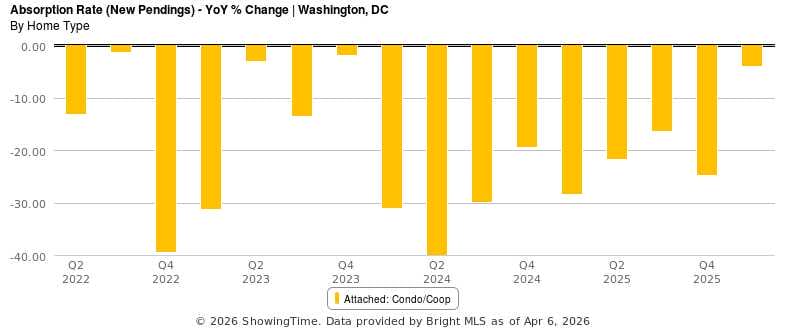
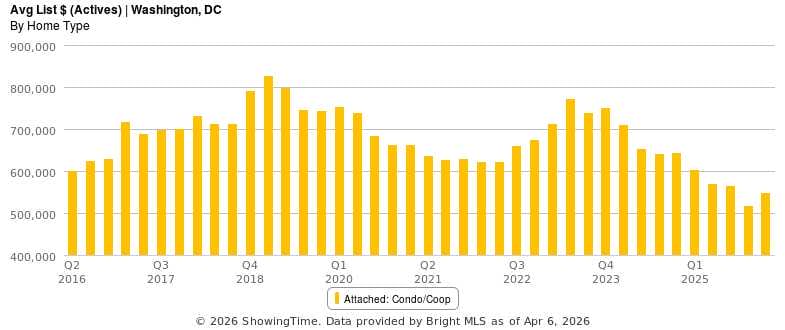
The absorption rate for DC condos has declined year-over-year for 16 quarters straight and 23 out of the past 26 quarters.
What this means: It is difficult to find buyers for DC condos
Washington DC Condo Inventory Declined Slightly
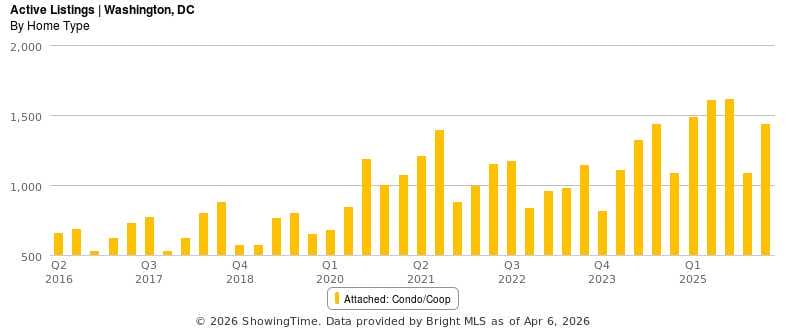
Total inventory declined by 3.4% year-over-year, the first quarterly drop since Q4 2023. Still, there were great than 2x more condos for sale in DC in Q1 2026 than Q1 2020
What this means: Motivated sellers must compete aggressively with each other for buyers
Washington DC Condos Keep Getting Cheaper
The average price of a DC condo listed for sale is 9.4% less than it was in Q1 2025 and ~9% less than it was ten years ago.
What this means: Even lowering the price won’t guarantee a buyer
If you’d like to discuss buying, selling, investing, or renting, don’t hesitate to reach out to me at [email protected].
We have access to the most pre and off-market listings across the DMV of any brokerage and are happy to share what’s available with anybody who asks.
Below are some of our team’s pre/off-market listings, details and additional listings available by request:
- Westover – 4BR/2BA/2,000sqft – Detached Single Family (2000) – 23rd St N Arlington VA 22205
- Green Valley – 5BR/4.5BA/3,000sqft – Detached Single Family (2020) – 24th St S Arlington VA 22206
- Ballston – 4BR/3.5BA/2,400sqft – Townhouse (2008) – N George Mason Dr Arlington VA 22203
- Ballston – 4BR/3.5BA+office/4,000 sqft – Four Townhouses (2026/2027) – 11th St N Arlington VA 22201
- Rosslyn – 2BR/2BA/1,800sqft – Condo (2021) – 1781 N Pierce St Arlington VA 22209
- Rosslyn – 3BR/2.5BA/2,400sqft – Condo (1986) – 1530 Key Blvd Arlington VA 22209
- Williamsburg – 6BR/5.5BA/5,500 sqft – Detached Single Family (2026) – 27th St N Arlington VA 22207
- Yorktown – 6BR/6.5BA/6,000+ sqft – Detached Single Family (2026) – N Greencastle St Arlington VA 22207
Eli and his team believe that your real estate needs should be managed by advisors, not salespeople. Their mission is to guide, educate, and advocate for their clients through real advice, hands-on support, and personalized service.
-

 Nebraska5 minutes ago
Nebraska5 minutes agoCarriker Chronicles: Sean Callahan on Matt Rhule’s Critical Year 4 with Nebraska Football
-

 Nevada11 minutes ago
Nevada11 minutes agoChanges could be made to Nevada’s ‘Black Book’ this week
-

 New Hampshire17 minutes ago
New Hampshire17 minutes agoHiker who set out in warm spring weather found dead after snowstorm in New Hampshire mountains
-

 New Jersey23 minutes ago
New Jersey23 minutes ago2028 New Jersey ATH has ‘great experience’ on visit to Syracuse
-

 New Mexico29 minutes ago
New Mexico29 minutes agoGovernor establishes Energy Affordability and Grid Reliability Council – 13-member council designed to protect ratepayers, modernize the grid – Office of the Governor – Michelle Lujan Grisham
-
North Carolina35 minutes ago
NC State’s 2026 Atlantic hurricane forecast calls for an average season with 12 to 15 named storms
-

 North Dakota41 minutes ago
North Dakota41 minutes agoValue of North Dakota oil rises as Iran war upends markets – KVRR Local News
-

 Ohio47 minutes ago
Ohio47 minutes agoNWSL announces expansion to Columbus, Ohio