In addition to the Surface Pro and Surface Laptop, Microsoft announced a crop of Copilot Plus PCs from all the major OEMs. Here are all the Copilot Plus PCs announced at Microsoft’s Surface event on Monday.
Technology
Google Home app gets much-needed redesign with interactive buttons
The Google House app is getting a recent design that ought to make it much more intuitive, in response to a report from 9to5Google. The upcoming 2.49 replace will allow you to work together along with your units from a single display, resembling the machine management panel on telephones with Android 11 and up.
Judging by the replace’s launch notes on the App Retailer, it appears Google is hoping to make the app much more user-friendly than what it’s proper now, saying it ought to aid you “rapidly discover what you’re searching for, dim your appropriate lights, and alter the music quantity in a snap.” Extra particularly, you’ll have the ability to faucet on a tool to show it on or off, slide left or proper on sure components, like lights or audio system to make changes to brightness and quantity, in addition to lengthy press on a tool to see extra choices.
Google House acquired its final main design change in 2018 — and later added controls to vary the colour of your lights — however has largely remained the identical ever since. This has left us with a clunky app that forces us to faucet into every machine to make particular changes (though there are nonetheless some single-tap controls like turning issues on or off).
Google says the redesign will roll out “over the following few weeks,” and even having the newest model of the app on iOS or Android may not be sufficient to see the adjustments. Some customers, like former editor in chief of XDA-Builders Mishaal Rahman, have efficiently sideloaded the two.49.1.8 replace on Android and accessed the brand new settings.

Technology
A lot of new Copilot Plus PCs will hit shelves starting in June
/cdn.vox-cdn.com/uploads/chorus_asset/file/25456799/lcimg_2c03ed43_c1df_414a_9e67_8100cdf3d526.jpeg)
Acer Swift 14 AI
Not to be confused with the other Swift 14 laptops with AI chips, the Swift 14 AI is the only one with a Qualcomm Snapdragon X series processor. This one comes with either the base 12-core Snapdragon X Elite chip or the 10-core X Plus chip and goes up to 32GB of memory and 1TB of M.2 SSD storage.
Asus Vivobook S 15
Asus is starting its Copilot PC adventure with its Vivobook S 15. It will have two Qualcomm processor options — the base 12-core Snapdragon X Elite and 10-core Snapdragon X Plus — and both options will support 32GB onboard memory and 1TB of PCIe 4.0 SSD.
Dell XPS, Inspiron, and Latitude
Dell is releasing five Copilot Plus PCs with Snapdragon this year, starting with the XPS 13 and Inspiron 14 Plus (7441). The XPS will be configured with a midtier Snapdragon X Elite chip and up to 64GB of memory and 2TB of PCIe SSD storage and will have three display options: two IPS, one touch-enabled; and one OLED that’s also a touchscreen. The OLED will have the highest resolution — but lowest refresh rate — out of the display options.
Meanwhile, the Inspiron will have the Snapdragon X Plus, support up to 32GB of memory and up to 1TB of M.2 2230 SSD storage, and only one display option, an IPS touchscreen. The Dell Latitude 7455 will have both Snapdragon X Elite and Plus options with support for up to 32GB of memory and 1TB of M.2 2230 SSD storage.
HP OmniBook and EliteBook Ultra
Along with HP’s ProBook, its OmniBook and Elitebook have replaced its now-former Envy, Pavilion, and Dragonfly series in a huge renaming effort to clean up and organize HP’s laptop portfolio. The Omibooks will be the consumer-focused devices, while the Elitebooks will be commercial, or business-focused.
HP will start shipping its new OmniBook X AI and EliteBook Ultra AI next month, and their configurations will include a 12-core Snapdragon X Elite processor. The Elitebook only goes up to 16 GB of memory, but the OmniBook can handle up to 32GB.
Lenovo Yoga Slim and ThinkPad
The Lenovo Yoga Slim 7x 14 and ThinkPad 14s will come with Snapdragon X Elite processors. The Yoga Slim will be the cheaper of the two due to the lack of Enterprise features that come with the business-oriented ThinkPad. Both will have OLED displays, but the ThinkPad will support up to 64GB of memory, while the Yoga Slim will support up to only 32GB.
Microsoft Surface Pro and Surface Laptop 6
The first Microsoft device to get its own Copilot Plus treatment is the Surface Pro. You’ll be able to get it with either the Snapdragon X Elite or X Plus processor, optional 5G connectivity, and either an IPS or OLED display.
There’s also the Surface Laptop 6, which also comes with either the Elite or Plus Snapdragon chips, and up to 64GB of memory and 1TB of SSD storage.
Samsung Galaxy Book4 Edge
Samsung’s first three Copilot Plus PCs are all under the name Galaxy Book4 Edge. There’s one 14-inch model and two 16-inch models, all with Snapdragon X Elite processors, 2880 x 1800 AMOLED touchscreens, and 16GB of RAM.
All of these PCs are available for preorder now and will start shipping on June 18th.
Technology
How to know if your computer got hacked, what to do next

Have you ever had that sinking feeling that something’s not quite right with your computer? Maybe it’s running slower than usual or there are new icons on your desktop that you don’t recognize. Well, you might not be just imagining things; you could have been hacked.
While the first reaction may be to panic, the best possible first step if you think you’ve been hacked is to disconnect your computer from the internet and take a deep breath. If you’ve got antivirus software already installed, run the scan immediately. But don’t worry just yet. Before you start fretting about cyberthieves and lost data, let’s take a moment to walk through some crucial steps together. From running a trusty antivirus scan to the nitty-gritty of browser settings and remote access – this is your go-to guide for outsmarting those pesky hackers.
GET SECURITY ALERTS, EXPERT TIPS – SIGN UP FOR KURT’S NEWSLETTER – THE CYBERGUY REPORT HERE
A woman grabbing her computer in frustration (Kurt “CyberGuy” Knutsson)
Were you hacked?
1. Run antivirus software ASAP
When you’re running any antivirus scans or troubleshooting, start from the actual antivirus software program. Don’t follow pop-ups or notifications. If there is indeed a compromise, it should show up on the dashboard of the antivirus software program.
Preventative:
- Keep your antivirus software updated. Hackers are coming up with new viruses often, so if you are up to date, you’re less likely to be compromised. Or the virus is more likely to get caught.
- Be familiar with your antivirus software notifications and alerts, so if you ever get a pop-up or notification, you’ll be more apt to notice fake ones.
- Write down the contact information of the antivirus software you’ve installed and have it near the computer.
If you feel pretty confident that you’ve unfortunately been hacked, but your antivirus scan comes up empty, take a break and call customer service of antivirus software directly. Do not follow links to have a rep call you. Use the number you’ve written down, and call them directly so you know you’re not being duped.
If you don’t have antivirus software installed, make sure to install one and do a computer scan. You can find our top recommendations here.
ASK ANY TECH QUESTION AND GET KURT’S FREE CYBERGUY REPORT NEWSLETTER HERE

A man typing on keyboard (Kurt “CyberGuy” Knutsson)
HOW TO RECOVER A HACKED FACEBOOK ACCOUNT
2. Reformat or reset to factory settings
Sometimes a virus or other nefarious entities have overrun the computer so badly that you might need to simply reformat or reset it to factory settings. If you’ve uninstalled or deleted suspicious programs or applications only to have them reload upon restarting your computer, you may simply need to start from scratch. This is why it is crucial to have recent backups of your data. Our article, “How to securely get rid of your old PC or Mac,” outlines how to reset to factory settings or reformat your computer.
EXPERT TIPS, LEGIT REVIEWS. GET THE FREE CYBERGUY REPORT NEWSLETTER
3. Delete settings or extensions on browsers or uninstall and reinstall browsers completely
There have been many times I have gone to help my mom with her online accounts, only to be inundated with pop-ups, redirects or random links on her browser bar or menu. It turned out that she had either accidentally downloaded extensions that embedded themselves in the browser or, worse, changed the browser setting to open a spammy website as her main search engine or landing page. You can go to settings or preferences and delete extensions you do not recognize. But if these settings or extensions keep reappearing after deleting and restarting the browser, it is likely a bigger problem. Then, uninstall the browser and see if you can reinstall it. If that brings up the same settings again, then it could be a much more invasive virus or malware that needs to be addressed with an antivirus scan or assistance from a professional.
HOW TO OUTSMART CRIMINAL HACKERS BY LOCKING THEM OUT OF YOUR DIGITAL ACCOUNTS
4. Turn off or restrict remote access
While it is harder for hackers to access your computer if it is completely turned off, if you have allowed remote access, a hacker just needs your computer to be hooked up to a network or the internet in order to take over your device and turn it on.
To prevent remote access to your PC:
- Click the Windows Start button
- Input Remote Desktop settings in the search bar
- In the Remote Desktop settings, ensure that the slider under “Enable Remote Desktop” is set to Off.
- Review your current processes in Task Manager (Ctrl+Alt+Del) for any unusual or suspicious activities
To prevent remote access on Macs:
- Click the Apple logo icon in the top left corner.
- Click System Settings
- Tap General
- Click the Sharing icon
- Scroll down and uncheck the boxes next to Remote Login and Remote Management to prevent unauthorized remote access.

A woman on her laptop (Kurt “CyberGuy” Knutsson)
HOW HACKERS CAN CRAFT AN ATTACK FROM YOUR SOCIAL MEDIA PROFILE
5. Review your activity monitor on your computer and network traffic patterns
Periodically, checking your computer’s activity monitor to check which programs are running and what is using up the most bandwidth is a healthy practice. It will teach you to spot any programs or traffic that is unusual or if someone else is connecting to your computer remotely.
To review this activity on your PC:
- Go to Control Panel
- Click Administrative Tools
- In Event viewer, look for the events that are related to startup and shutdown. Any shutdown will be listed there and which program or user-initiated that startup or shutdown. This way, you can see if these actions are that of a virus or an update process.
To review this activity on your Mac:
- Go to the menu bar on the top left when you first log on to your account.
- Select Go
- In the drop-down menu, select Utilities
- When a menu pops up, one of the first options should be Activity Monitor.
Or:
- Go to your Applications folder on your dock (usually located on the bottom or right-hand side of the screen)
- Go to Utilities folder
- Select Activity Monitor

A man putting in his username and password on tablet (Kurt “CyberGuy” Knutsson)
Top 3 preventative measures to not get hacked
1. Turn on 2-factor authentication
While it may seem like a pain to enter a code received via email or text each time you sign in, this extra step is crucial for security. By activating two-factor authentication, you create a barrier against unauthorized access. Even if a hacker discovers your email or username, they won’t get far without the unique code.
Each login attempt triggers a notification, alerting you to potential threats. Repeated failed attempts will secure your account by either locking it or sending you an alert. In the event of suspicious activity, you can swiftly use a trusted device to reset your password and inform the service provider. It’s a small price to pay for significant protection against cyberthreats.

A man backing up his computer (Kurt “CyberGuy” Knutsson)
2. Have strong antivirus software
The best way to protect yourself from clicking malicious links that install malware in an attempt to get access to your private information is to have antivirus protection installed on all your devices. This can also alert you of any phishing emails or ransomware scams. Plus, think of it like having a digital bodyguard – always on the lookout, always ready to defend you from cyberthreats. Get my picks for the best 2024 antivirus protection winners for your Windows, Mac, Android & iOS devices.
3. Configure your email settings
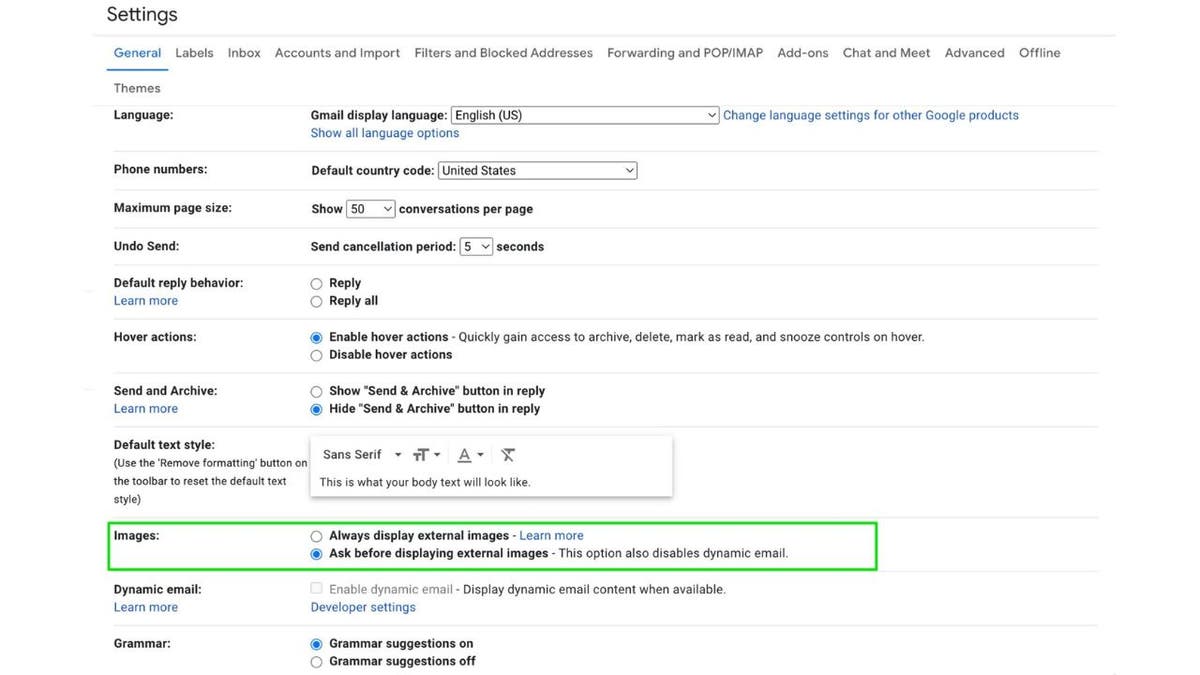
Configure email settings to not automatically images or attachments (Kurt “CyberGuy” Knutsson)
If you configure your email settings to not automatically load content such as images or attachments, then it is harder for viruses or other malware to be automatically downloaded or accidentally opened. If you also have emails received first in rich text format, you can choose which emails load fully with images once you realize it is from a trusted source.
Gmail desktop:
- Click the settings gear icon
- Choose See all settings
- Under the General tab, scroll to the Images section.
- Select Ask before displaying external images
- Scroll to the bottom of the page and click Save Changes
Gmail mobile:
- Tap the hamburger menu (3 horizontal lines)
- Select Settings
- Choose the account you want to manage
- Scroll to the Images section and select Ask before displaying external images.
Apple mail:
- First, click on Mail in your dock at the bottom of your screen
- Then click on Mail in the upper left of your screen
- Click Settings
- Go to the Viewing tab
- Uncheck Load remote content in messages
Outlook desktop (PC):
- Click File
- Choose Options
- Select Trust Center
- Click Trust Center Settings
- Under Automatic Download, check the option that says Don’t download pictures automatically in standard HTML email messages or RSS items.
Outlook desktop (Mac):
- Open Outlook
- Click Preferences
- Under Email select Reading
- Choose Security
- Select Never to prevent image downloads
Yahoo Mail desktop:
- Click Settings.
- Choose More Settings.
- Click Viewing email.
- Under Show images in messages, select Ask before showing external images.
Start Mail desktop:
Please note that the exact wording of the menu items and options can vary based on the version of Start Mail you are using.
- Open Start Mail
- Click on the Settings icon
- Navigate to the Email section
- Look for the Images or Privacy settings
- Choose the option to Ask before displaying external images or a similar setting that controls the automatic downloading of pictures.
These steps should help enhance your email security by giving you control over which images are displayed, thereby reducing the risk of malware being automatically downloaded or opened. Always ensure your email application is updated to the latest version for the best security practices.
Looking for private and secure email solutions? See Best Private and Secure Email Providers 2024
QUICK TIPS. EXPERT INSIGHTS. CLICK TO GET THE FREE CYBERGUY REPORT NEWSLETTER
Data recovery: Protecting your information against loss
This may not seem relevant to an article about hacking, but having your data off your computer and safely on an external hard drive or the cloud will give you more options if you think you’ve been hacked. If you need help deciding what type of data backup would be best for you, please take a look at these articles:
If a hack is bad enough, sometimes a complete wipe of your system is the only way to salvage your computer. If you have a safe copy of your data, while it might be inconvenient, you will not lose all your data. Also, if you keep more sensitive data off your more frequently used computer, then your data is less likely to be compromised if you get hacked.
Kurt’s key takeaways
At the end of the day, being hacked is a massive inconvenience and can potentially lead to data loss or theft. But don’t lose hope. There are steps you can take to outsmart those pesky hackers and keep your devices secure. The key is staying vigilant and taking preventative measures like using strong antivirus software, enabling two-factor authentication and regularly backing up your data. That way, if you do get hacked, you’ll have a recent backup to rely on and can simply wipe your device clean without losing everything.
It’s also crucial to keep an eye out for any suspicious activity on your computer or network. If something seems off, don’t hesitate to run a full antivirus scan and review your activity monitor for any unauthorized access or programs running in the background. Remember, hackers are always coming up with new tricks, so it’s an ongoing battle to stay one step ahead. But by following the tips outlined here, you’ll be well on your way to keeping your digital life secure and hack-free. Stay vigilant, my friends.
Can you share a personal story where being proactive about computer security paid off or, conversely, where neglecting it led to issues? Let us know by writing us at Cyberguy.com/Contact.
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter.
Ask Kurt a question or let us know what stories you’d like us to cover.
Follow Kurt on Facebook, YouTube and Instagram.
Answers to the most asked CyberGuy questions:
Copyright 2024 CyberGuy.com. All rights reserved.
Technology
Apple’s next AirTag could arrive in 2025
/cdn.vox-cdn.com/uploads/chorus_asset/file/22461385/vpavic_4547_20210421_0067.jpg)
You may not have even thought about replacing your AirTag yet, but Bloomberg reports that Apple is working on a new one that could arrive in mid-2025. The new AirTag will reportedly feature an updated chip with better location tracking — an improvement it might need as competition among tracking devices ramps up.
By the time Apple rolls out its refreshed AirTag, the Bluetooth tracking landscape will look a lot different on both Android and iOS. Last month, Google revealed its new Find My Device network, which lets users locate their phones using signals from nearby Android devices. Even Life360, the safety service company that owns Tile, is creating its own location-tracking network that uses satellites to locate its Bluetooth tags.
In last week’s iOS 17.5 update, Apple finally started letting iPhones show unwanted tracking alerts for third-party Bluetooth tags. If an unknown AirTag or other third-party tracker is found with an iPhone user, they’ll get an alert and can play a sound to locate it. The feature is part of an industry specification created to prevent stalking across iPhones and Android devices. Several companies that make Bluetooth tracking devices, including Chipolo, Pebblebee, and Eufy are on board with the new standard.
-

 News1 week ago
News1 week agoSkeletal remains found almost 40 years ago identified as woman who disappeared in 1968
-

 World1 week ago
World1 week agoIndia Lok Sabha election 2024 Phase 4: Who votes and what’s at stake?
-

 Movie Reviews1 week ago
Movie Reviews1 week ago“Kingdom of the Planet of the Apes”: Disney's New Kingdom is Far From Magical (Movie Review)
-

 World1 week ago
World1 week agoUkraine’s military chief admits ‘difficult situation’ in Kharkiv region
-

 Politics1 week ago
Politics1 week agoTales from the trail: The blue states Trump eyes to turn red in November
-

 World1 week ago
World1 week agoBorrell: Spain, Ireland and others could recognise Palestine on 21 May
-

 World1 week ago
World1 week agoCatalans vote in crucial regional election for the separatist movement
-
 Politics1 week ago
Politics1 week agoNorth Dakota gov, former presidential candidate Doug Burgum front and center at Trump New Jersey rally













