Technology
Fake Google security page can turn your browser into a spying tool

NEWYou can now listen to Fox News articles!
A new phishing scam is tricking people into installing malware by pretending to be a Google security check. The page looks convincing and tells you that your Google account needs additional protection. It walks you through a simple setup process that appears to strengthen your security and protect your devices.
If you follow those steps, you may end up installing what looks like a harmless security tool. In reality, security researchers say the page installs a malicious web app that can spy on your device. It can steal login verification codes, watch what you copy and paste, track your location and quietly send internet traffic through your browser.
The most troubling part is that nothing is technically hacked. Instead of exploiting a software flaw, attackers simply trick you into granting the permissions they need. Once that happens, your own browser can start working for them without you realizing it.
Sign up for my FREE CyberGuy Report. Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CYBERGUY.COM newsletter.
THE #1 GOOGLE SEARCH SCAM EVERYONE FALLS FOR
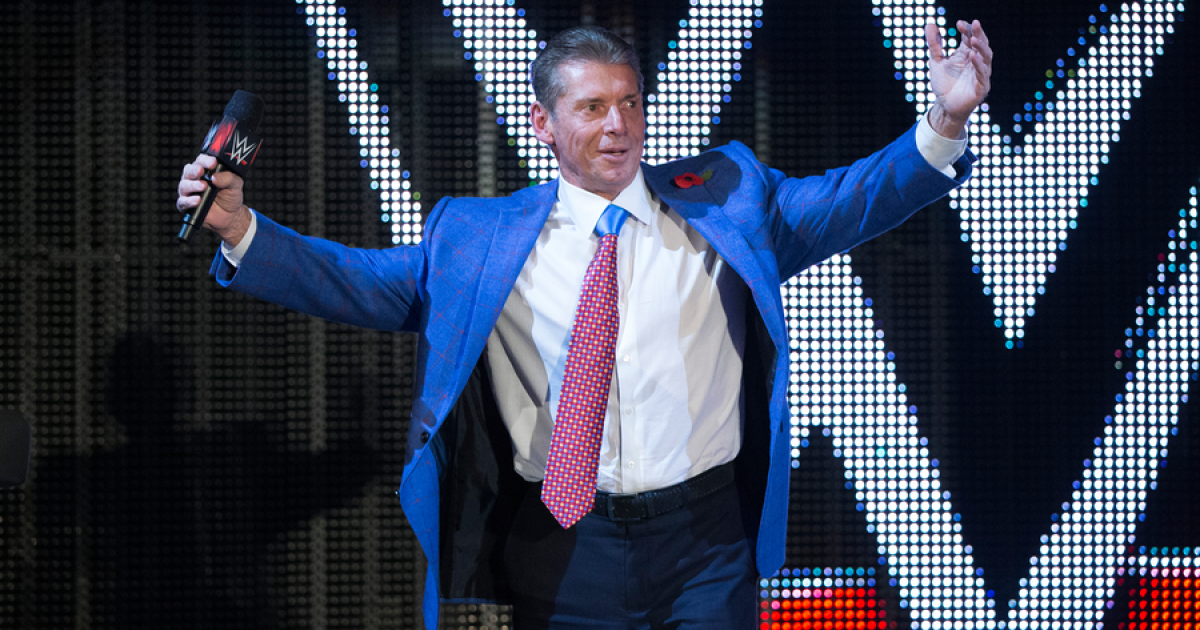
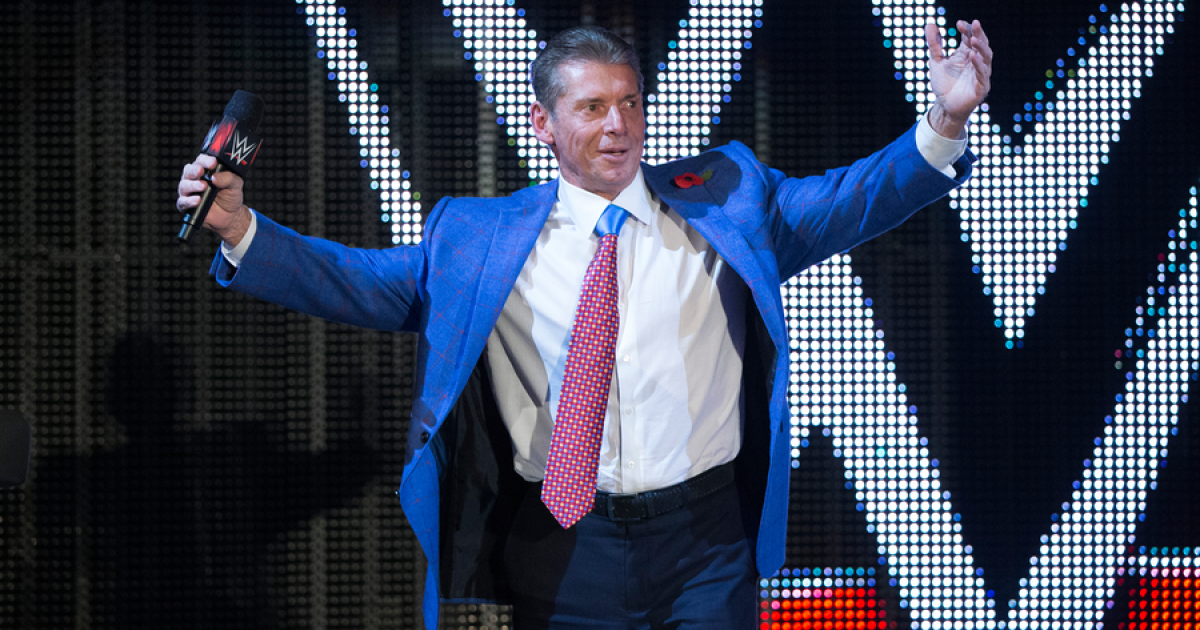
The fake site mimics a Google security page and urges visitors to complete a quick “account protection” setup. (AP Photo/Don Ryan, File)
All about the fake Google security page
Security researchers at Malwarebytes, a cybersecurity company, recently discovered a phishing website that pretends to be part of Google’s account protection system. The site uses the domain google-prism[.]com and presents what looks like a legitimate security page asking you to complete a short verification process. Visitors are told they should complete a four-step setup to improve their account protection. The page explains that these steps will help secure your Google account and protect your devices from threats. During the process, the site asks you to approve several permissions and install what it claims is a security tool.
The tool it installs is actually a Progressive Web App. This type of application runs through your browser but behaves like a regular app on your computer. It opens in its own window, can send notifications and can run tasks in the background. Once installed, the malicious web app can collect contacts, read information you copy to your clipboard, track GPS location data and attempt to capture one-time login codes sent to your phone. These codes are commonly used when you sign in to accounts that use two-factor authentication.
The fake security page may also offer an Android companion app described as a “critical security update.” Researchers found that this app requests 33 permissions, including access to text messages, call logs, contacts, microphone recordings and accessibility features. Those permissions give attackers the ability to read messages, capture keystrokes, monitor notifications and maintain control over parts of the device. Even if the Android app is never installed, the web app alone can still collect sensitive information and quietly run activity through your browser.
How it works and why it matters to you
The scam works because it looks like something you would normally trust. Many people expect security alerts from the services they use, especially when it comes to protecting email or cloud accounts. Attackers take advantage of that trust by presenting the fake page as a helpful security feature. When you approve the permissions and install the web app, you are essentially giving the attackers access to certain parts of your device. One of the main things they try to capture is one-time passwords. These are the short codes you receive when logging in to accounts that require two-factor authentication.
If attackers manage to capture those codes while also knowing your password, they may be able to break into your accounts. That could include your email, financial services, or cryptocurrency wallets, depending on which accounts you use. The malware also watches what you copy and paste. Many people copy cryptocurrency wallet addresses before sending digital currency, and those addresses can be valuable to criminals. The malicious app can collect that information and send it back to the attackers.
Another feature allows attackers to route internet requests through your browser. This means they can run online activity through your device so it appears to come from your home network. The app can also send notifications that look like security alerts or system warnings. When you click those notifications, the app opens again and gains another opportunity to capture information such as login codes or clipboard data.
Google says built-in protections can block the threat
After learning about the phishing campaign, we asked Google about the malicious site and whether users are protected.
A Google spokesperson told CyberGuy that several built-in security systems are designed to stop threats like this before they cause harm.
“We can confirm that Safe Browsing in Chrome warns any user who tries to visit this site. Chrome also shows a confirmation dialog whenever anyone attempts to download an APK. Android users are automatically protected against known versions of this malware by Google Play Protect, which is on by default on Android devices with Google Play Services.”
Google also said that its current monitoring shows no apps containing this malware are available on the Google Play Store.
ANDROID MALWARE HIDDEN IN FAKE ANTIVIRUS APP
Even if malicious apps are installed from outside official stores, Google says Android devices still have an additional layer of protection. Google Play Protect can warn users or block apps known to exhibit malicious behavior, including apps installed from third-party sources.
However, it is important to note that Google Play Protect may not be enough. Historically, it isn’t 100% foolproof at removing all known malware from Android devices, which is why we recommend additional strong antivirus software to detect malicious downloads, suspicious browser activity and phishing attempts before they cause serious damage. It acts as an early warning system that helps block dangerous apps and websites before they gain access to your device or your data.
During the process, users are prompted to approve permissions and install what appears to be a security tool. (iStock)
Get my picks for the best 2026 antivirus protection winners for your Windows, Mac, Android & iOS devices at Cyberguy.com.
7 ways to protect yourself from fake security pages
If you ever come across a suspicious “security check” like this, a few simple habits can help you avoid falling into the trap and protect your accounts and devices.
1) Never run security checks from random websites
Google does not ask you to install security tools through pop-ups or unfamiliar websites. If a page claims your account needs a security check, close the tab and go directly to Google’s official account page by typing the address yourself. Visiting the real account settings page prevents attackers from redirecting you to a fake site.
2) Check website addresses carefully before trusting them
Phishing pages often use domains that look similar to real companies. Attackers rely on people clicking quickly without paying attention to the address bar. If the website address is not an official Google domain, do not trust it. Even a small change in the spelling can indicate a fake site designed to steal information.
3) Remove suspicious web apps from your browser
If you installed an app through a website and it opens like a standalone program, check your browser’s installed apps or extensions list. Remove anything you do not recognize or do not remember installing. Uninstalling the app immediately prevents it from collecting more information or running commands through your browser.
4) Check your Android phone for unfamiliar apps
Researchers say the malicious Android app may appear as “Security Check” or “System Service.” If you see unfamiliar apps with these names, review the permissions they request and remove them if they look suspicious. Apps asking for extensive permissions such as SMS access, accessibility features, and microphone control should always be investigated.
5) Use a password manager for your accounts
A password manager helps you create and store strong, unique passwords for every account you use online. If attackers obtain one password, they will not automatically gain access to other accounts. Password managers can also help prevent you from entering credentials on fake sites because they usually refuse to auto-fill on lookalike domains.
Check out the best expert-reviewed password managers of 2026 at Cyberguy.com
6) Enable two-factor authentication whenever possible
Two-factor authentication (2FA) adds an extra layer of protection beyond your password. Even though this attack tries to capture SMS verification codes, many services allow you to use authenticator apps instead. These apps generate login codes on your device and make it much harder for attackers to intercept them.
7) Monitor your accounts for unusual activity
If you think you interacted with a suspicious security page, keep a close eye on your accounts over the following days. Watch for login alerts, password reset emails, or transactions you do not recognize. Acting quickly after suspicious activity can help prevent attackers from gaining full control of your accounts.
Pro tip: Reduce how easily scammers can target you
Scammers often gather personal details from data broker sites to make phishing messages look more convincing. A data removal service can help remove your personal information from many of those databases, reducing the amount of information criminals can use to impersonate companies or craft targeted scams.
Check out my top picks for data removal services and get a free scan to find out if your personal information is already out on the web by visiting Cyberguy.com
Get a free scan to find out if your personal information is already out on the web: Cyberguy.com.
Researchers say the malicious web app could collect login codes, clipboard data and other sensitive information. (Felix Zahn/Photothek via Getty Images)
Kurt’s key takeaway
Attackers are changing tactics. Instead of breaking into systems through technical flaws, they are relying on convincing security messages that persuade people to install tools themselves. All of us rely on familiar brands like Google when making security decisions, and attackers know that. Preventing these scams will likely require faster action against impersonation sites and stronger safeguards around what web apps are allowed to do once installed.
Should companies like Google be required to automatically block lookalike domains that pretend to run official security checks before people fall for them? Let us know by writing to us at Cyberguy.com
CLICK HERE TO DOWNLOAD THE FOX NEWS APP
Sign up for my FREE CyberGuy Report. Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CYBERGUY.COM newsletter.
Copyright 2026 CyberGuy.com. All rights reserved.

Technology
Backrooms is a certified blockbuster with a $38 million opening day

The Kane Parsons’ film Backrooms is expected to earn up to $90 million in its opening weekend after pulling down $38 million on Friday alone. That’s not only above expectations, but absolutely obliterates A24’s previous opening weekend record of $25.5 million for Alex Garland’s Civil War. It’s also a better opening day than The Mandalorian and Grogu, which only pulled down $33.7 million on its way to a total $81.6 million for the weekend.
That also means that Backrooms is an incredibly profitable movie, with an estimated $10 million budget. By comparison, the latest Star Wars disappointment cost $165 million and was considered affordable compared to other entries in the series.
While Backrooms hasn’t received quite as much universal praise as fellow low-budget horror breakout Obsession, it’s still largely getting positive reviews. It also adds to the growing number of YouTube creators (including Obsession’s Curry Barker) who have proven to be successful box office draws.
Technology
Cab-less electric trucks hit Ohio roads

NEWYou can now listen to Fox News articles!
A freight truck with no driver, no cab and no one sitting behind the wheel is starting to sound more familiar. In fact, this summer, that is exactly what is happening on local roads in Marysville, Ohio.
EASE Logistics, an Ohio-based logistics company, is partnering with autonomous truck technology company Einride to deploy two cab-less electric trucks between EASE warehouse locations. The two companies recently announced the proof-of-concept service.
The trucks will operate on EASE property and local public roads. They will move goods between warehouse locations while the companies collect data on warehousing, distribution and transportation operations.
The project is part of the Ohio Department of Transportation’s DriveOhio Truck Automation Corridor Project, in partnership with the Indiana Department of Transportation. The goal is to study how autonomous trucking affects operations, safety and freight efficiency.
Sign up for my FREE CyberGuy Report
- Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox.
- For simple, real-world ways to spot scams early and stay protected, visit CyberGuy.com – trusted by millions who watch CyberGuy on TV daily.
Plus, you’ll get instant access to my Ultimate Scam Survival Guide free when you join.
AI TRUCK SYSTEM MATCHES TOP HUMAN DRIVERS IN MASSIVE SAFETY SHOWDOWN WITH PERFECT SCORES
Autonomous cab-less electric trucks are beginning real-world freight testing this summer on local roads in Marysville, Ohio, as EASE Logistics and Einride launch a new pilot program. (Kurt “CyberGuy” Knutsson)
What are cab-less electric trucks?
These are not regular trucks with a driver waiting to take over. Einride’s vehicles are electric, autonomous and cab-less. That means there is no traditional driver’s seat, steering wheel area or cab built for a human operator.
The trucks use SAE Level 4 autonomous technology. In other words, the vehicle can drive itself under specific approved conditions without a human driver inside.
However, the trucks will still have human oversight. A remote operator will monitor them from off-site and can intervene when needed. The companies say that setup helps keep operations running safely and smoothly during the test.
Where will the autonomous trucks operate?
The trucks will move freight between EASE Logistics warehouses in Marysville, Ohio. They will operate during the summer of 2026 on private property and local public roads.
That detail makes a difference because many autonomous vehicle tests happen in controlled settings. This project moves closer to normal freight work. These trucks will operate inside daily logistics
EASE says the deployment will generate data on how autonomous trucks affect warehouse movement, distribution timing and transportation operations. The companies want to see how this technology performs in the real world, where freight schedules and traffic conditions rarely behave perfectly.
THE ROAD TO PROSPERITY WILL BE PAVED BY AUTONOMOUS TRUCKING
EASE Logistics and Einride will operate driverless electric freight trucks between Ohio warehouse locations while collecting data on safety, efficiency and logistics operations. (Kurt “CyberGuy” Knutsson)
Why Ohio is testing cab-less electric trucks
Ohio has become an active testing ground for truck automation. This deployment extends the Ohio Department of Transportation and DriveOhio’s Truck Automation Corridor Project, in partnership with the Indiana Department of Transportation. The project is designed to evaluate how autonomous technology affects operations, safety and freight efficiency.
EASE President and CEO Peter Coratola, Jr., said, “EASE is proud to continue advancing the Truck Automation Corridor Project alongside DriveOhio and innovative partners like Einride.” He added, “Deployments like this help move autonomous trucking from controlled pilots into daily freight operations, where safety, reliability, and efficiency can be evaluated at scale.”
This also marks EASE Logistics’ third autonomous trucking deployment with DriveOhio. That puts the company among a small group of logistics providers testing multiple autonomous freight platforms in live operations.
How safe are cab-less electric trucks?
When people hear “driverless truck,” their first thought may not be efficiency. It may be, “What happens if something goes wrong?”
That reaction is fair. These vehicles are large, heavy and operate near the public. So safety will shape how people judge this project.
Einride CEO Roozbeh Charli said, “Deploying these autonomous trucks in daily logistics operations with EASE reflects years of rigorous development and real-world validation.” He added, “Safety is not a feature we add to our technology; it is the foundation everything is built on.”
The companies also say a remote operator monitors the trucks off-site and can intervene if needed. That detail helps, but the public will still want clear answers about routes, oversight, emergency response and how remote operators step in. Those answers will become more important as autonomous trucks leave closed test areas and enter everyday traffic.
Why companies want driverless freight
For logistics companies, the appeal is easy to understand. Electric autonomous trucks could help move freight with fewer emissions, more predictable scheduling and tighter warehouse coordination.
Short warehouse-to-warehouse routes also make sense for early autonomous deployments. The route is limited. The operation is easier to study. The company can collect useful data without starting with long-haul trucking across several states.
Still, the rollout will need to prove itself. Trucks must handle traffic, road conditions, pedestrians and unexpected behavior from human drivers. Those moments will test whether autonomous freight can deliver on its promise.
The future of autonomous trucking
Autonomous trucking has moved from bold promise to real-world testing. Yet the industry still has to earn public confidence.
This Ohio deployment gives EASE, Einride and transportation officials a chance to gather useful data. It also gives the public a closer look at what driverless freight looks like.
The cab-less design may be the most striking part. Removing the cab signals a bigger shift. These trucks are built around the idea that the vehicle, software and remote operations team can handle the job.
That marks a major change in how freight has worked for generations.
TESLA BUILDS A CAR WITH NO STEERING WHEEL. NOW WHAT?
Ohio officials are expanding autonomous freight testing with cab-less electric trucks operating on public roads under remote human supervision this summer. (Kurt “CyberGuy” Knutsson)
What this means to you
You may not live near Marysville, Ohio. Still, this test matters because it shows where freight transportation is heading.
If the project works well, more companies could look at autonomous trucks for warehouse-to-warehouse routes. That could change how goods move before they ever reach store shelves or your front door.
It could also raise new questions for workers. Logistics companies may need more people who can monitor, maintain and manage autonomous systems. At the same time, drivers and warehouse workers will want honest answers about how these trucks could affect jobs over time.
For consumers, the biggest issue may be trust. People will want proof that these vehicles can operate safely around regular traffic. They will also want transparency when something goes wrong.
Join CyberGuy Live: Lock Down Your Phone in 30 Minutes (Saturday, June 13, 10 am ET)
Your phone holds your email, passwords, photos, banking apps and personal data. In this free, live online class, Kurt the CyberGuy will walk you step by step through simple phone security fixes you can do in real time. You’ll learn how to improve your privacy settings, spot the latest phone scams, use trusted security tools and walk away with a simple checklist to stay protected. Register here: CyberGuyLive.com
CLICK HERE TO DOWNLOAD THE FOX NEWS APP
Kurt’s key takeaways
Cab-less electric trucks on Ohio roads may sound alarming at first. But this project shows how quickly autonomous freight is moving into real logistics work. The EASE and Einride deployment still has plenty to prove. Safety, public trust, worker impact and day-to-day reliability will all matter. However, this summer’s test could give the trucking industry a clearer look at what comes next. Driverless freight may start with short warehouse routes. Over time, it could reshape how goods move across the country.
Would you feel comfortable sharing the road with a cab-less electric truck if no driver was inside, but a remote operator was watching from miles away? Let us know by writing to us at CyberGuy.com.
Sign up for my FREE CyberGuy Report
- Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox.
- For simple, real-world ways to spot scams early and stay protected, visit CyberGuy.com – trusted by millions who watch CyberGuy on TV daily.
- Plus, you’ll get instant access to my Ultimate Scam Survival Guide free when you join.
Copyright 2026 CyberGuy.com. All rights reserved.
Technology
Nvidia, Microsoft, and Arm are all teasing Nvidia’s new N1X laptop processors

It’s the world’s worst kept secret that Nvidia is about to announce its own Arm-powered laptop chips at Computex this weekend, and now Microsoft, Nvidia, and Arm are all openly teasing the announcement. The Windows and Nvidia GeForce accounts on X both posted “A new era of PC” earlier today, and now Arm has followed up with an identical post.
All three posts include coordinates pointing to where Computex is hosted in Taipei. Nvidia is holding a Computex keynote in Taipei at 8PM PT / 11PM ET on Sunday night, where it’s rumored to be announcing its new N1 and N1x laptop chips.
These Arm-powered Nvidia processors have been long-rumored, with reports earlier this year suggesting that both Lenovo and Dell have been preparing new laptops with the N1X chips. We first heard rumors about Nvidia’s laptop processors in 2023, and Dell CEO Michael Dell hinted at the possibility of an AI PC with Nvidia during an interview in 2024.
Nvidia’s entry into Windows on Arm will mean Qualcomm will no longer have an exclusive license for Microsoft’s Windows 11 Arm variant of its operating system. That’s good news for laptop competition, even if Qualcomm is trying to keep entry-level laptops affordable with its new Snapdragon C platform.
-

 Technology11 minutes ago
Technology11 minutes agoBackrooms is a certified blockbuster with a $38 million opening day
-

 World14 minutes ago
World14 minutes agoHamas struggles to fill leadership ranks as Israel hunts Oct 7 terrorists
-

 Politics19 minutes ago
Politics19 minutes agoAnti-ICE agitator charged with allegedly biting officers during Delaney Hall clashes
-

 Health26 minutes ago
Health26 minutes agoWhat to do if someone is having a stroke, after Jill Biden revealed debate-night fears
-

 Sports29 minutes ago
Sports29 minutes agoDispatch audio reveals what was heard inside Josh Jacobs’ home before alleged domestic violence arrest
-

 Technology34 minutes ago
Technology34 minutes agoCab-less electric trucks hit Ohio roads
-
 Business41 minutes ago
Business41 minutes agoVince McMahon and others are sanctioned for destroying evidence in WWE shareholder lawsuit
-

 Entertainment44 minutes ago
Entertainment44 minutes agoReview: Alicia Keys’ glorious music fuels blazing ‘Hell’s Kitchen’ at the Hollywood Pantages











