If you live in Los Angeles, you are probably already intimately familiar with Watch Duty, the free app that shows active fires, mandatory evacuation zones, air quality indexes, wind direction, and a wealth of other information that everyone, from firefighters to regular people, have come to rely on during this week’s historic and devastating wildfires.
Technology
Abandoning doggy doo? DNA will sniff you out and expose you

Hey there, pet owners. Do you have a furry friend who likes to leave “surprises” on the ground?
Well, you had better start scooping up after them because DNA testing is coming to sniff out the culprits.
A couple walking a dog (Kurt “CyberGuy” Knutsson)
The poop scoop on DNA testing
You read that right. Some apartment complexes and homeowners associations are now requiring residents to have their dogs’ DNA tested. The idea is to create a database of doggy DNA profiles. So, if any unscooped poop is found on the premises, they can connect it to the guilty party and issue a fine.
GET SECURITY ALERTS, EXPERT TIPS – SIGN UP FOR KURT’S NEWSLETTER – THE CYBERGUY REPORT HERE
It might sound a bit extreme, but let’s be real. Nobody wants to step in a steaming pile of dog doo on their way to the mailbox. And for property managers, dealing with unclaimed dog waste is a real headache (and a smelly one at that).

A woman walking her dog (Kurt “CyberGuy” Knutsson)
BEST PET TECH GIFT GUIDE
The pioneers of poop policing
This DNA testing trend isn’t brand new, but it’s definitely gaining traction. In 2019, some apartment complexes in Denver were already on board with a service called PooPrints. Catchy name, right?
The way it works is simple. Residents register their dogs and provide a cheek swab for DNA testing. Once the database is set up, any rogue piles can be matched to the offending pup, and the owner gets slapped with a fine. In some places, that fine can be as high as $250, a pretty penny for not picking up your pet’s pennies, if you catch my drift.
CLICK HERE FOR MORE U.S. NEWS

A man walking his dog (Kurt “CyberGuy” Knutsson)
5 BEST PET TRACKERS
The bark spreads nationwide
Fast-forward to today, and PooPrints (or similar services) have spread to communities across all 50 states. Utah, in particular, has embraced the idea with many apartment complexes hopping on the DNA doggy doo bandwagon.
And now it seems like the Oak Meadows complex in Connecticut is the latest to join the ranks of poop policing. Residents there will need to get their dog’s DNA tested in July or face a daily $25 fine for non-compliance. Yikes. While some residents view it as an invasion of privacy, others support it as a way to curb the problem of uncollected dog waste.

A dog being walked on a leash (Kurt “CyberGuy” Knutsson)
HOW TO FLY WITH YOUR DOG WHEN MONEY IS NO OBJECT
Kurt’s key takeaways
Look, I get it. Having to DNA test your dog just so you’ll clean up after it seems a bit over the top. But, at the same time, leaving dog poop around is just plain inconsiderate (and gross). Maybe these DNA measures are what it takes to finally get some pet owners to be responsible and scoop that poop. After all, nobody wants to live in a community that’s littered with canine landmines. So, dear fellow dog owners, do us all a favor and carry some doggy bags on your walks and pick up after your pup. That way, we can avoid this whole DNA drama altogether and keep our neighborhoods clean and green (and stink-free).
Do you view mandatory pet DNA testing as an invasion of privacy or a reasonable measure? Let us know by writing us at Cyberguy.com/Contact
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter
Ask Kurt a question or let us know what stories you’d like us to cover
Follow Kurt on his social channels
Answers to the most asked CyberGuy questions:
Copyright 2024 CyberGuy.com. All rights reserved.

Technology
Amazon Prime will shut down its clothing try-on program
/cdn.vox-cdn.com/uploads/chorus_asset/file/23935558/acastro_STK103__01.jpg)
Given the combination of Try Before You Buy only scaling to a limited number of items and customers increasingly using our new AI-powered features like virtual try-on, personalized size recommendations, review highlights, and improved size charts to make sure they find the right fit, we’re phasing out the Try Before You Buy option, effective January 31, 2025. Of course, customers will continue to enjoy fast, free shipping, with easy, free returns on our full apparel selection.
Technology
Fox News AI Newsletter: Tech leaders' message to Biden
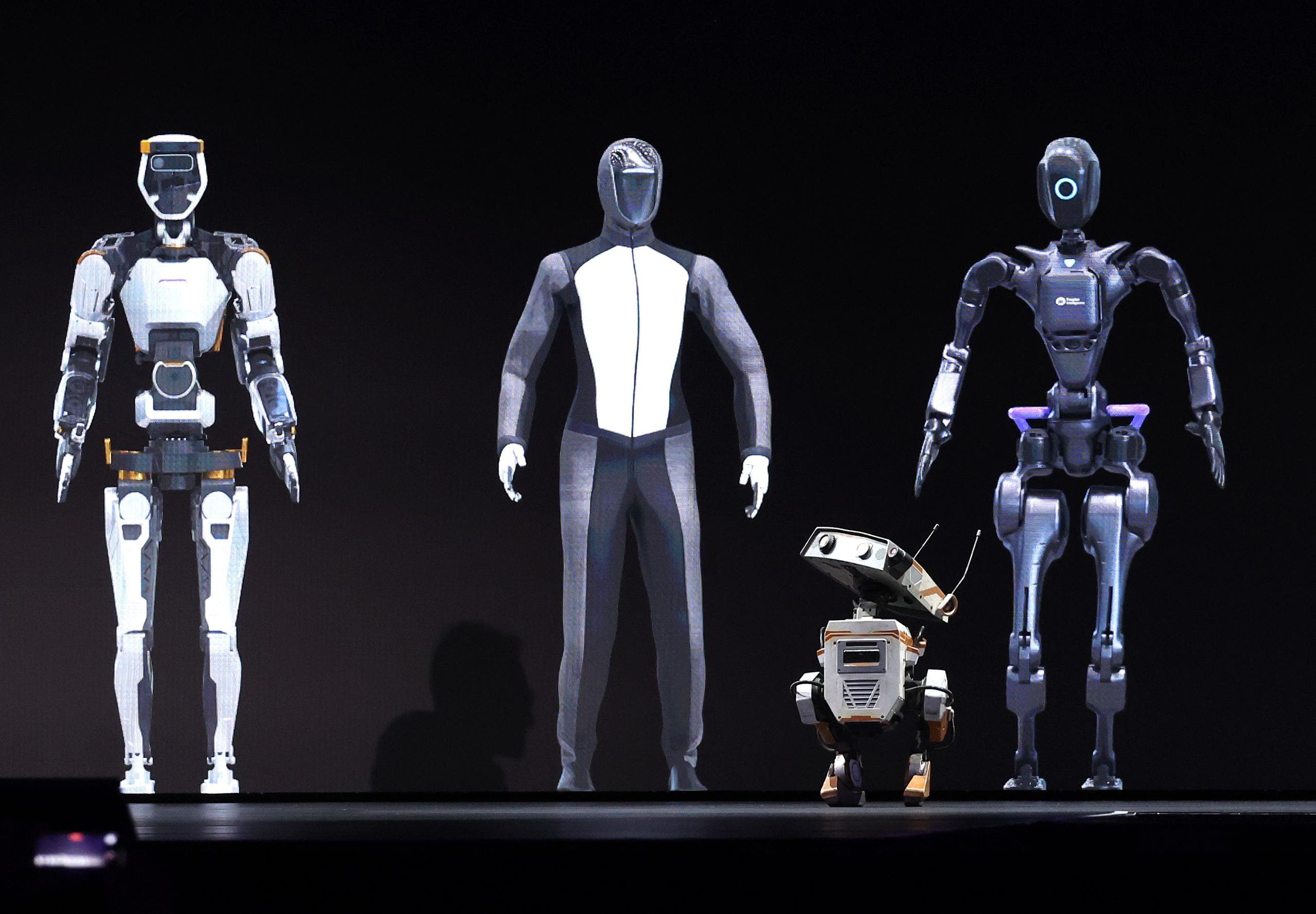
Nvidia is developing real-world robots that are equipped with artificial intelligence capabilities. (Justin Sullivan/Getty Images)
Welcome to Fox News’ Artificial Intelligence newsletter with the latest AI technology advancements.
IN TODAY’S NEWSLETTER:
– Tech industry leaders urge Biden not to cement rule they say could diminish US global leadership on AI
– Sam Altman responds to lawsuit, allegations of abuse from sister
– As a Berkeley professor, I see the impact H-1B visas and AI have on students’ job opportunities
– Top tech stealing the show at CES 2025
PUSH BACK: The new rule, which industry leaders say could come as early as the end of this week, effectively seeks to shore up the U.S. economy and national security efforts by adding new restrictions on how many U.S.-made artifical intelligence products can be deployed across the globe.

Jensen Huang, co-founder and chief executive officer of Nvidia Corp., speaks during the Nvidia GPU Technology Conference (GTC) in San Jose, Calif., on Monday, March 18, 2024. (David Paul Morris/Bloomberg via Getty Images)
‘UTTERLY UNTRUE’: Open AI CEO Sam Altman on Tuesday responded to a lawsuit in which his sister accused him of sexually abusing her for nearly a decade. Altman, along with his mother and two brothers, issued a joint statement denying the claims of his sister, Ann Altman.

Sam Altman, chief executive officer of OpenAI, speaks during the Bloomberg Technology Summit in San Francisco on Thursday, June 22, 2023. (David Paul Morris/Bloomberg via Getty Images)
LOW COST LABOR: The H-1B visa program was intended to bring in specialized talent from abroad, but instead it has become a tool for employers to hire lower-cost labor for ordinary jobs.

Illustrative picture showing an application for the United States of America work visa H1B with a pen.
BEST OF CES: Get ready for some pretty cool innovations that are lighting up CES 2025, the world’s biggest annual tech event. From AI-powered smart glasses to revolutionary TVs and mind-blowing gadgets, this year’s show is proving that the future isn’t just knocking. It’s bursting through the door.
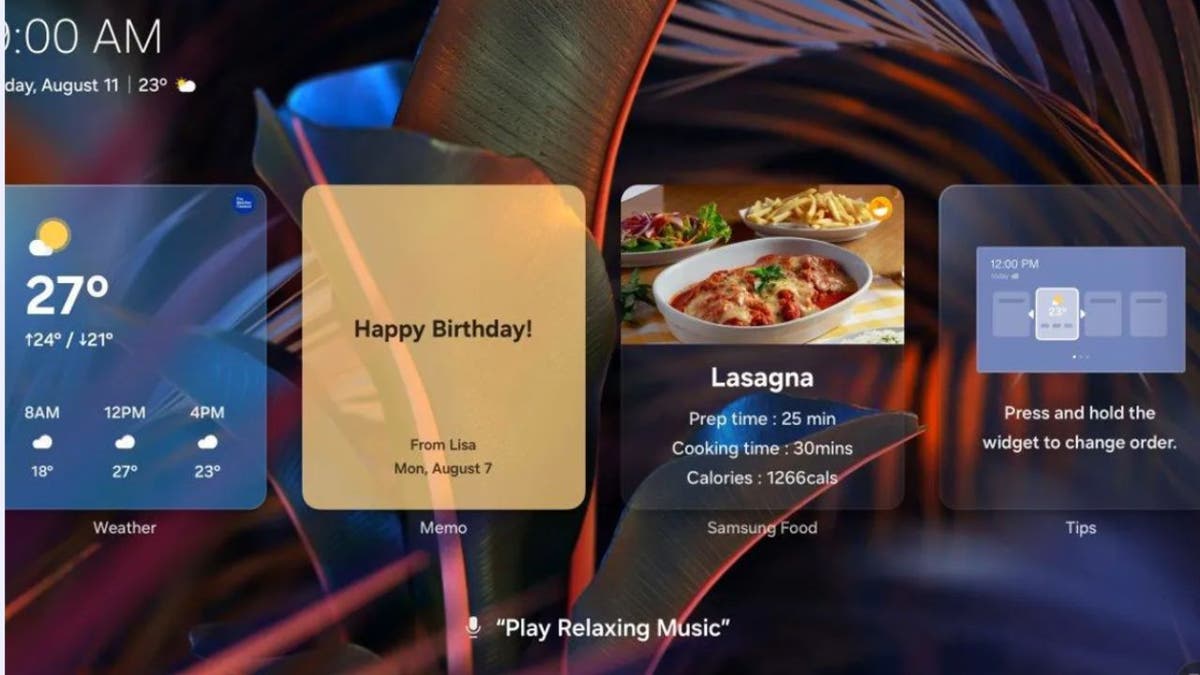
Samsung Food app. (Kurt “CyberGuy” Knutsson)
Subscribe now to get the Fox News Artificial Intelligence Newsletter in your inbox.
FOLLOW FOX NEWS ON SOCIAL MEDIA
Facebook
Instagram
YouTube
Twitter
LinkedIn
SIGN UP FOR OUR OTHER NEWSLETTERS
Fox News First
Fox News Opinion
Fox News Lifestyle
Fox News Health
DOWNLOAD OUR APPS
Fox News
Fox Business
Fox Weather
Fox Sports
Tubi
WATCH FOX NEWS ONLINE
Fox News Go
STREAM FOX NATION
Fox Nation
Stay up to date on the latest AI technology advancements and learn about the challenges and opportunities AI presents now and for the future with Fox News here.
Technology
How Watch Duty’s wildfire tracking app became a crucial lifeline for LA
/cdn.vox-cdn.com/uploads/chorus_asset/file/25824833/STKB309_WATCH_DUTY_B.jpg)
Watch Duty is unique in the tech world in that it doesn’t care about user engagement, time spent, or ad sales. The 501(c)(3) nonprofit behind it only cares about the accuracy of the information it provides and the speed with which the service can deliver that information. The app itself has taken off, rocketing to the top of Apple’s and Google’s app stores. Over 1 million people have downloaded it over the last few days alone.
The elegance of the app lies in its simplicity. It doesn’t scrape user data, show ads, require any kind of login, or track your information. Its simple tech stack and UI — most of which is maintained by volunteer engineers and reporters — has likely helped save countless lives. While Watch Duty is free to use, the app accepts tax-deductible donations and offers two tiers of membership that unlock additional features, like a firefighting flight tracker and the ability to set alerts for more than four counties.
With plans to expand the service across the United States, as well as overseas and into other emergency services, Watch Duty may eventually replace some of the slower and less reliable local government alert systems for millions of people.
Photo by Lokman Vural Elibol / Anadolu via Getty Images
An app born from fire
The idea for Watch Duty came to cofounder John Mills while he was trying to protect his off-grid Sonoma County home from the Walbridge fire in 2020. He realized there wasn’t a single source for all the information people needed to protect themselves from the blaze, which ultimately killed 33 people and destroyed 156 homes. John and his friend David Merritt, who is Watch Duty’s cofounder and CTO, decided to build an app to help.
“This came out of an idea that John had, and he talked to me about it four years ago,” Merritt tells The Verge. “We built the app in 60 days, and it was run completely by volunteers, no full-time staff. It was a side project for a lot of engineers, so the aim was to keep it as simple as possible.”
Fire reporting is piecemeal at best in fire-prone areas and frequently scattered across platforms like Facebook and X, where fire departments and counties have verified pages sharing relevant updates. But increasingly, social media platforms are putting automated access for alert services behind paywalls. Governments also use a wide variety of alert systems, causing delays that can cost lives, especially in fast-moving fires like the Palisades and Eaton fires that have forced evacuations for more than 180,000 people. And sometimes, these government-run alerts are sent out mistakenly, causing mass confusion.
Watch Duty simplifies all that for millions of people.
“We view what we are doing as a public service,” says Merritt. “It is a utility that everyone should have, which is timely, relevant information for their safety during emergencies. Right now, it’s very scattered. Even the agencies themselves, which have the best intentions, their hands are tied by bureaucracy or contracts. We partner with government sources with a focus on firefighting.”
“We view what we are doing as a public service.”
One of the biggest issues around fires, in particular, is that they can move quickly and consume large swaths of land and structures in minutes. For example, the winds that drove the Palisades fire to spread to more than 10,000 acres reached 90 miles per hour on Tuesday. When minutes matter, the piecemeal alert system that Watch Duty replaces can cause delays that cost lives.
“Some of the delivery systems for push notifications and text messages that government agencies use had a 15-minute delay, which is not good for fire,” says Merritt. “We shoot to have push notifications out in under a minute. Right now, 1.5 million people in LA are getting push notifications through the app. That’s a lot of messages to send out in 60 seconds. In general, people are getting it pretty much all at the same time.”
A simple tech stack
For Watch Duty, this kind of mass communication requires reliable technology as well as a group of dedicated staff and skilled volunteers. Merritt says that Watch Duty relies on a number of corporate partners with whom it has relationships and contracts to provide its service.
“We shoot to have push notifications out in under a minute.”
The app is built on a mix of technology, including Google’s cloud platform, Amazon Web Services, Firebase, Fastly, and Heroku. Merritt says the app uses some AI, but only for internal routing of alerts and emails. Reporters at Watch Duty — those who listen to scanners and update the app with push notifications about everything from air drops to evacuation updates — are mostly volunteers who coordinate coverage via Slack.
“All information is vetted for quality over quantity,” he says. “We have a code of conduct for reporters. For example, we never report on injuries or give specific addresses. It’s all tailored with a specific set of criteria. We don’t editorialize. We report on what we have heard on the scanners.”
According to Merritt, the app has 100 percent uptime. Even though it started with volunteer engineers, the nonprofit has slowly added more full-time people. “We still have volunteers helping us, but it’s becoming more on the internal paid staff as we grow, as things get more complex, and as we have more rigorous processes,” he says.
“All information is vetted for quality over quantity.”
He says there are no plans to ever charge for the app or scrape user data. The approach is kind of the Field of Dreams method to building a free app that saves people’s lives: if you build it well, the funding will come.
“It’s the antithesis of what a lot of tech does,” Merritt says. “We don’t want you to spend time in the app. You get information and get out. We have the option of adding more photos, but we limit those to the ones that provide different views of a fire we have been tracking. We don’t want people doom scrolling.”
Photo by FREDERIC J. BROWN / AFP via Getty Images
Collecting information in the era of Trump
Watch Duty relies heavily on publicly available information from places like the National Weather Service and the Environmental Protection Agency. Should the incoming Trump administration decide to execute on threats to dismantle and disband the EPA (which monitors air quality) and the National Oceanic and Atmospheric Administration, the parent agency to the National Weather Service, such moves would impact Watch Duty’s ability to operate.
Even still, Merritt is optimistic. “We will be pretty well insulated from any change to policy,” he says. “We are either buying that information ourselves already or we are happy to buy it, and we will take that cost on. The fact that we’re soon going to be covering the entire US will defray the cost of anything that shifts from a policy perspective. Our operation costs are mostly salaries. We are trying to hire really good engineers and have a really solid platform. If we need to raise a grant to buy data from the National Weather Service, then we will.”
Regardless of what the next administration does, it’s clear that Watch Duty has become a critical and necessary app for those in Southern California right now. The app currently covers 22 states and plans to roll out nationwide soon.
“We got 1.4 million app downloads in the last few days,” according to Merritt. “I think we have only received 60 support tickets, so that shows that something is working there. We are really just focused on the delivery of this information.”
-

 Politics1 week ago
Politics1 week agoNew Orleans attacker had 'remote detonator' for explosives in French Quarter, Biden says
-

 Politics1 week ago
Politics1 week agoCarter's judicial picks reshaped the federal bench across the country
-

 Politics1 week ago
Politics1 week agoWho Are the Recipients of the Presidential Medal of Freedom?
-

 Health6 days ago
Health6 days agoOzempic ‘microdosing’ is the new weight-loss trend: Should you try it?
-

 World1 week ago
World1 week agoSouth Korea extends Boeing 737-800 inspections as Jeju Air wreckage lifted
-
/cdn.vox-cdn.com/uploads/chorus_asset/file/25822586/STK169_ZUCKERBERG_MAGA_STKS491_CVIRGINIA_A.jpg)
/cdn.vox-cdn.com/uploads/chorus_asset/file/25822586/STK169_ZUCKERBERG_MAGA_STKS491_CVIRGINIA_A.jpg) Technology3 days ago
Technology3 days agoMeta is highlighting a splintering global approach to online speech
-

 World1 week ago
World1 week agoWeather warnings as freezing temperatures hit United Kingdom
-

 News1 week ago
News1 week agoSeeking to heal the country, Jimmy Carter pardoned men who evaded the Vietnam War draft














