As useful as connected devices like video doorbells and smart lights are, it’s wise to exercise caution when using connected tech in your home, especially after years of reading about security camera hacks, fridge botnet attacks, and smart stoves turning themselves on. But until now, there hasn’t been an easy way to assess a product’s security chops. A new program from the Connectivity Standards Alliance (CSA), the group behind the smart home standard Matter, wants to fix that.
Technology
We’re one step closer to a global cybersecurity standard for smart home devices
/cdn.vox-cdn.com/uploads/chorus_asset/file/25342556/Screenshot_2024_03_18_at_12.09.17_PM.png?ssl=1)
Announced this week, the CSA’s IoT Device Security Specification is a baseline cybersecurity standard and certification program that aims to provide a single, globally recognized security certification for consumer IoT devices.
Device makers who adhere to the specification and go through the certification process can carry the CSA’s new Product Security Verified (PSV) Mark. If that security camera or smart lightbulb you’re buying carries the mark, you’ll know it has met requirements to help secure it from malicious hacking attempts and other intrusions that could impact your privacy.
“It’s a huge step forward to have a global consumer IoT security certification. It’s so much better than not having one,” Steve Hanna, Infineon
“Research continually shows that consumers rate security as an important device purchase driver, but they don’t know what to look for from a security perspective to make an informed purchase decision,” Eugene Liderman, director of mobile security strategy at Google, tells The Verge. “Programs like this will give consumers a simple, easily identifiable indicator to look for.”
Liderman is part of the CSA working group that defined the 1.0 spec for the program, which has been developed by over 200 member companies of the CSA. These include (along with Google) Amazon, Comcast, Signify (Philips Hue), and several chipmakers such as Arm, Infineon, and NXP.
According to Tobin Richardson, CEO of the CSA, products carrying the PSV Mark could start to appear as soon as this holiday shopping season.
One cybersecurity mark to rule them all
The CSA’s announcement on March 18th follows last week’s news that the FCC has approved implementing its new cybersecurity labeling program for consumer IoT devices in the US. Both programs are voluntary, and the CSA’s label doesn’t compete with the US Cyber Trust Mark. Instead, it goes a step further, taking all of the US requirements and adding cybersecurity baselines from similar programs in Singapore and Europe. The end result is a single specification and certification program that can work across multiple countries (see sidebar).
Richardson says the goal is for the CSA’s PSV Mark to be recognized by governments, so manufacturers can go through just one certification process to sell in all the major markets. This could reduce cost and complexity for manufacturers and potentially bring more choice to consumers.
The PSV Mark has been recognized by the Cyber Security Agency of Singapore, and the CSA says it is working on mutual recognition with similar programs in the US, EU, and the UK. “It’s very likely, and with some [countries], it’s a certainty,” says Richardson. “It’s mainly a matter of tying up some paperwork.”
To get the PSV Mark, devices must comply with the IoT Device Security Specification 1.0 and go through a certification program that involves answering a questionnaire and providing accompanying evidence to an authorized test laboratory. Highlights of the requirements include:
- Unique identity for each IoT Device
- No hardcoded default passwords
- Secure storage of sensitive data on the device
- Secure communications of security-relevant information
- Secure software updates throughout the support period
- Secure development process, including vulnerability management
- Public documentation regarding security, including the support period
According to the CSA, the voluntary program applies to most connected smart home devices — including lightbulbs, switches, thermostats, and security cameras — and can be applied retroactively to products in the market. Along with the PSV Mark, “A printed URL, hyperlink, or QR code on the mark gives consumers access to more information about the device’s security features,” the CSA says in its press release.
The program is focused specifically on device security — making sure the physical device itself can’t be accessed — rather than privacy. “But there is a close linkage in that you can’t have privacy without security,” says Richardson. While security impacts privacy, this program doesn’t offer many requirements around how a manufacturer uses the data a device collects. The CSA has a separate Data Privacy Working Group dealing with that can of worms.
Better security, but still not perfect
The current iteration of the program isn’t a silver bullet to solve IoT device security concerns. Steve Hanna of Infineon Technologies, a 25-year cybersecurity researcher and chair of the CSA working group for the program, told The Verge there’s still more he’d like to see incorporated. “But we have to crawl, walk, and then run,” he says. “It’s a huge step forward to have a global consumer IoT security certification. It’s so much better than not having one.”
Google’s Liderman also points out that meeting the minimum security standard doesn’t guarantee a device is vulnerability-free. “We greatly believe that the industry needs to raise the bar over time, especially for sensitive product categories,” he says.
The CSA plans to keep the specification updated, requiring companies to recertify at least every three years. Additionally, Richardson says there will be a requirement for an incident response process, so if a company encounters a security issue — such as Wyze’s recent problems — it must fix those before it can be recertified.
An API could allow a smart home platform app to alert you to a device’s security status before it can join your network
To address concerns about misuse of the label, Hanna says the CSA will have a database of all certified products on its website so you can cross-check a company’s claims. He also says there are plans to make the information available in an API, which could allow your smart home platform app to alert you to a device’s security status before it can join your network.
Hanna cautions against setting expectations too high. “Some companies are excited about it to recognize the work they have already done, but we shouldn’t expect every product to have this,” he says. Some may find they have problems that mean they can’t get certified, he says. “If or when these become required by governments, that’s where the rubber hits the road.”
A voluntary program may seem like a finger in the dam, but it does solve two basic problems. For manufacturers, it makes it simpler to comply with regulations from multiple countries in one step, while for consumers, it opens an avenue to information about what type of security practices a company adheres to.
“Without a label or a mark, it can be difficult as a consumer to make a purchasing decision based on security,” says Hollie Hennessy, an IoT cybersecurity expert at tech analyst firm Omdia. While the program being voluntary could be a barrier to adoption, Hennessy says her firm’s research indicates people are more likely to purchase a device with privacy and security labeling.
Ultimately, Hennessy believes that a combination of standards and certifications like this, along with regulations and legislationis needed to solve consumer concerns about privacy and security in connected devices. But this move is a big step in the right direction.

Technology
Microsoft is disabling Office 2019 for Mac next month

Microsoft’s Office 2019 apps for Mac will stop working next month, because the company isn’t renewing a certificate that validates Office licenses. Owners of Office 2019 for Mac are being warned they’ll have to purchase Office 2024 or a Microsoft 365 subscription if they want to continue editing documents.
Microsoft previously promised that “all your Office 2019 apps will continue to function,” when it announced end of support in 2023. The company then quietly updated that support note last month to remove the mention of apps continuing to function, replacing it with “Rest assured that all your Office 2019 apps won’t lose any data.”
Starting on July 13th, Office 2019 for Mac and Office 2021 for Mac will both run in “reduced functionality mode,” allowing people to open files but not edit, save, or create new documents. The reduced functionality will impact Word, Excel, PowerPoint, Outlook, and OneNote.
While Microsoft is providing a certificate update for Office 2021 as it’s still supported until October 13th, 2026, the company is leaving Office 2019 for Mac users out in the cold as support for these apps ended a few years ago. “Office 2019 for Mac reached end of support on October 10, 2023, and no longer receives updates,” says Microsoft. “Because Office 2019 cannot be updated to the required version, this issue cannot be resolved by updating or reinstalling Office 2019 for Mac.”
JimmyTech points out that old versions of Microsoft 365 apps on Mac and iOS will also be affected by this certificate issue, but a simple update will fix it for those users.
Microsoft regularly ends support of software and there’s always the risk you could run into issues running older apps or versions of Windows. It’s still surprising to not see Microsoft make an exception here though, particularly because this certificate issue breaks the main functionality of an app you’ve paid a one-time license fee for.
Technology
Android fake call detection warns you about scams

NEWYou can now listen to Fox News articles!
You know that little moment when your phone rings and the name on the screen makes you drop everything?
Maybe it says your spouse, your daughter, your boss or your best friend. You answer because you trust the name. Then the voice sounds familiar too.
That is exactly what makes the latest phone scams so dangerous.
Android’s fake call detection can warn you when a caller may be pretending to be someone saved in your contacts. (Silas Stein/Picture Alliance)
Scammers no longer have to call from a strange number. They can spoof a trusted contact’s phone number. Then they can use AI voice tools to sound like someone you know. Android is now rolling out a new feature called fake call detection to help warn you when that familiar call may be a fake.
FAKE AGENT PHONE SCAMS ARE SPREADING FAST ACROSS THE US
Join CyberGuy Live: Lock Down Your Phone in 30 Minutes (Saturday, June 13, 10 am ET)
- Your phone holds your email, passwords, photos, banking apps and personal data. In this free, live online class, Kurt the CyberGuy will walk you step by step through simple phone security fixes you can do in real time. You’ll learn how to improve your privacy settings, spot the latest phone scams, use trusted security tools and walk away with a simple checklist to stay protected. Register here: CyberGuyLive.com
What is Android fake call detection?
Android fake call detection is a new protection built into Phone by Google. It is designed to spot suspected spoofed calls when both people on the call use Phone by Google.
Think of it as your phone quietly asking, “Is this call really coming from that person’s device?” If the answer looks suspicious, your phone can show a warning and advise you to hang up. That small alert could stop a scam before fear, panic or confusion takes over.
ANDROID SECURITY UPGRADES OUTSMART SCAMS AND PROTECT YOUR PRIVACY
How Android fake call detection works
The feature works automatically in the background. You do not need to answer a quiz, scan a code or press a button during the call. When a trusted contact calls you, their phone sends a silent confirmation signal to your phone. That signal helps prove the call really came from their device.
If a scammer spoofs your contact’s number, that confirmation signal may be missing. Your phone then checks with your contact’s actual device. If the real device says it is not placing a call, your screen can warn you that the call may be fake.
The system uses end-to-end encrypted RCS technology, so the check happens privately. You can also turn the feature off in Phone by Google settings.
AI DEEPFAKE ROMANCE SCAM STEALS WOMAN’S HOME AND LIFE SAVINGS
Why fake calls are getting harder to spot
For years, caller ID gave people a sense of control. If the name looked familiar, most of us felt safer picking up. That old habit now works in the scammer’s favor.
Scammers can use internet-based calling tools to spoof numbers. That means your phone may display the name of someone you trust, even though the call comes from somewhere else.
Then comes the AI voice trick. With today’s audio tools, scammers can make a fake voice sound shockingly real. They may pretend to be a family member in trouble, a bank employee warning about fraud or a manager asking for urgent help.
SCAMMERS EXPLOITED MOM’S FEARS TO STEAL HER ENTIRE LIFE’S SAVINGS
That combination makes the call feel personal and immediate. It also makes you more likely to act before you think.
Why Android is adding this protection now
Impersonation scams have become a major global problem. INTERPOL’s March 2026 Global Financial Fraud Threat Assessment cited impersonation fraud as one of the leading contributors to more than $400 billion in global losses.
In the U.S., impersonation scams remain one of the top fraud categories reported to the FTC. Losses reached $2.95 billion in 2024.
GLOBAL SCAM CRACKDOWN LEADS TO 276 ARRESTS
Those numbers tell you why this feature deserves attention. Scammers go where the money is. Right now, they know trusted voices and trusted names can open the door.
Which Android phones get fake call detection?
Google says fake call detection is rolling out globally in Phone by Google this month, starting with Pixel devices.
The feature is available on Android 12 and newer devices with Phone by Google, Contacts and Google Messages installed. It also requires RCS capability in Google Messages.
SAMSUNG MESSAGES ENDING? WHAT ANDROID OWNERS MUST KNOW
There is one key limitation. Both you and the person calling you must use Phone by Google for fake call detection to work.
Phone by Google already comes as the default phone app on many Android devices. If your phone uses a different calling app, you can install Phone by Google from the Play Store and set it as your default phone app.
How Android fake call detection protects you
This feature gives you an extra warning at the exact moment you need it most. That timing is important. Scam calls often rely on emotion. The caller may say someone got arrested, a loved one had an accident or a bank account faces an urgent threat.
SSA IMPERSONATION SCAMS ARE GETTING MORE PERSONAL
When the voice sounds familiar, your guard drops. A warning on your screen can interrupt that emotional rush. It gives you a reason to stop, hang up and verify the story another way.
What Android fake call detection cannot do
This new tool helps, but it cannot protect you from every scam. It may not work if the other person does not use Phone by Google. It also may not cover calls from businesses, unknown numbers or contacts using unsupported devices. So you still need basic scam rules.
If someone asks for money, gift cards, crypto, account codes or remote access to your device, hang up. Then call the person or company back using a number you already trust.
Also, never stay on the line just because the caller tells you to. That is one of the oldest pressure tactics in the scammer playbook.
A spoofed call can look familiar on your screen, even when it is really coming from a scammer. (Kurt CyberGuy Knutsson)
How to protect yourself from AI voice scams
AI voice scams work because they sound personal, urgent and believable, so your best defense is to slow the conversation down before you act.
1) Create a family safe word
Pick a simple word or phrase that only your close family knows. It should be easy to remember but hard for a scammer to guess. Then, if someone calls with an emergency and asks for money, ask for the safe word. If they cannot give it, hang up and verify the story another way.
9 WAYS SCAMMERS CAN USE YOUR PHONE NUMBER TO TRY TO TRICK YOU
2) Pause when the call feels urgent
Scammers want you scared because fear makes people act fast. That is why fake emergency calls often sound intense, emotional and rushed. Take a breath before you do anything. A real loved one, bank or employer will let you verify what is happening.
3) Call back using a trusted number
If a call feels suspicious, hang up. Then call the person back using a number saved in your contacts or one you know is real. Do not use a number, link or instruction the caller gives you. That could send you right back to the scammer.
4) Never send money or codes during the call
Do not send gift cards, crypto, wire transfers or payment app transfers because a caller sounds convincing. Also, never share a one-time passcode, PIN or account login code over the phone. Once scammers get that information, they can move fast.
5) Turn on scam protections on your phone
Use the built-in protections already available on your device. Pixel and Samsung users can enable Scam Detection in the Phone by Google app to help flag suspicious calls. Also, consider using strong antivirus software that includes AI-powered scam protection to help detect scams in texts, online content and deepfake videos. Keep an eye on call warnings too. If your phone tells you something looks risky, treat that alert seriously. Get my picks for the best 2026 antivirus protection winners for your Windows, Mac, Android & iOS devices at Cyberguy.com
6) Keep your phone apps updated
Update Phone by Google, Google Contacts and Google Messages when updates are available. These tools work best when your apps and phone software stay current. Updates often include security improvements, bug fixes and new scam protections.
Here’s how to check for updates on Android:
- Open the Google Play Store app.
- Tap your profile icon in the top right corner.
- Tap Manage apps & device.
- Under Updates available, tap See details.
- Look for Phone by Google, Google Contacts and Google Messages.
- Tap Update next to each app, or tap Update all.
You can also turn on automatic app updates by opening the Google Play Store app, tapping your profile icon, then going to Settings > Network preferences > Auto-update apps. From there, choose whether to update apps over Wi-Fi, over Wi-Fi or mobile data, with limited mobile data or not at all.
Kurt’s key takeaways
If a call feels urgent or suspicious, pause before you respond and verify it another way. (Tristan Spinski/The Washington Post via Getty Images)
Android’s fake call detection is a smart step in the fight against AI-powered phone scams. It recognizes something many people already know: the name on your caller ID no longer proves the person calling you is real. This feature gives Android users another layer of protection when scammers try to hijack trust. Still, the safest move remains simple. Slow down, verify the call and never let panic make the decision for you.
Should the government do more to stop scammers from using AI voices to impersonate the people you trust? Let us know by writing to us at CyberGuy.com
Sign up for my FREE CyberGuy Report
CLICK HERE TO DOWNLOAD THE FOX NEWS APP
- Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox.
- For simple, real-world ways to spot scams early and stay protected, visit CyberGuy.com – trusted by millions who watch CyberGuy on TV daily.
- Plus, you’ll get instant access to my Ultimate Scam Survival Guide free when you join.
Copyright 2026 CyberGuy.com. All rights reserved.
Technology
Congress just gave DHS another $70 billion

Congress narrowly voted to fund President Donald Trump’s mass deportation agenda, giving the Department of Homeland Security $70 billion over the next three years.
The house voted 214 to 212 in favor of the reconciliation bill Tuesday, following the Senate’s 52-47 vote last Friday morning. The vote fell largely along party lines. Sen. Lisa Murkowski (R-AK) was the only Senate Republican to vote against it. Rep. Tim Walberg (R-MI), initially voted against the bill — meaning it would have failed — but changed his vote after huddling with House Majority Leader Steve Scalise (R-LA) and Appropriations Chair Tom Cole (R-OK), according to The Hill. No Democrats voted in favor of the funding bill, which was done through a budget reconciliation process to avoid a Democratic filibuster.
In a speech on the House floor ahead of the Tuesday vote, Rep. Mary Gay Scanlon (D-PA) criticized Republicans for using the budget reconciliation process to avoid negotiating with Democrats, and emphasized ICE’s lack of popularity with the American people.
“At its core, this Republican reconciliation budget bill is a statement about priorities, and the priorities represented in this budget bill could not be more out of step with the needs and values of the American people,” Scanlon said.
Scanlon noted that DHS has yet to spend $100 billion of the nearly $200 billion it received under Trump’s One Big Beautiful Bill Act. She added that Trump has not only expanded ICE’s reach by increasingly going after legal immigrants but also weaponized DHS against its critics. The bill, she said, will “supercharge” Trump’s abuses.
After the House markup last Friday, Rep. Rosa DeLauro (D-CT), ranking member of the House Appropriations Committee, noted that the bill not only lacks sufficient reforms but also cuts funding for cybersecurity and TSA, whose workers went weeks without pay during the DHS shutdown.
The funding bill comes at a time of deep unpopularity for ICE. One recent poll found that just 33 percent of voters approve of how the agency is doing its job.
And it comes amid yet another threat from border czar Tom Homan to flood New York City with ICE agents. In an interview with Fox News on Monday, Homan said he would send “more ICE agents than you’ve ever seen” to New York City if the state government passed a bill limiting cooperation with DHS.
“Providing a quarter trillion dollars to an administration promising that the public ‘ain’t seen shit yet’ when it comes to mass deportation is a historic mistake,” Todd Schulte, president of the immigration reform group FWD.us, said in a statement. “Supercharging the funding for these already out of control systems will come with terrible human consequences and continue to be met with increasing opposition from voters.”
Correction, June 9th: A previous version of this story said Rep. Tim Walberg voted against the funding bill. He initially voted against it but then changed his vote to support it.
Update, June 9th: This story has been updated to include comment from FWD.us president Todd Schulte.
-
 Politics2 minutes ago
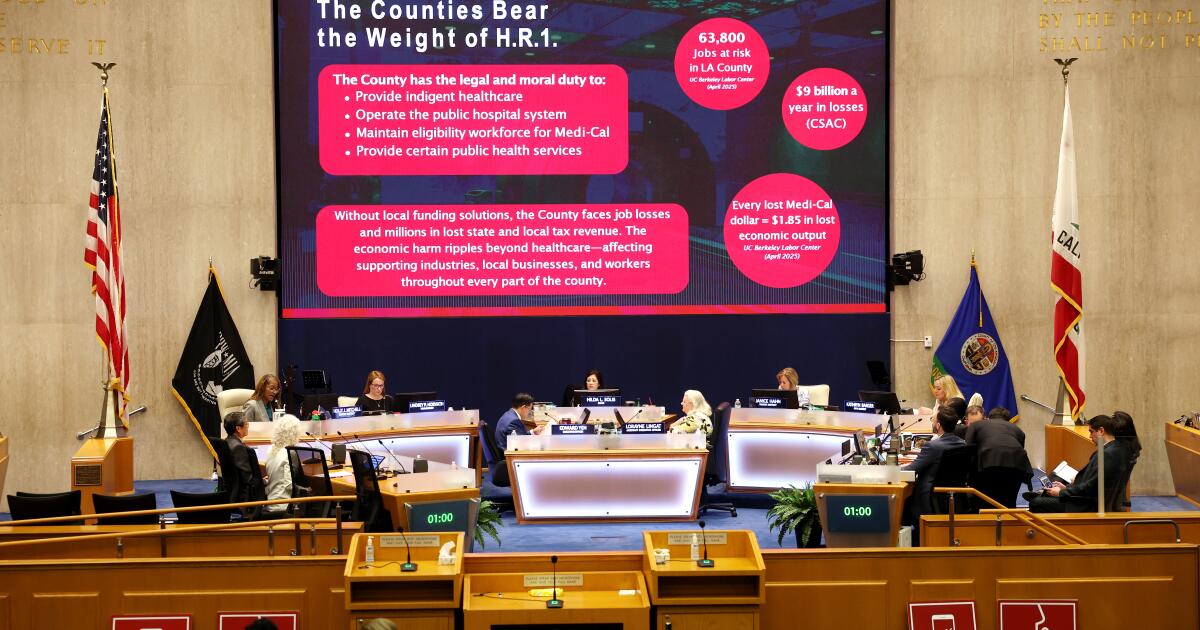
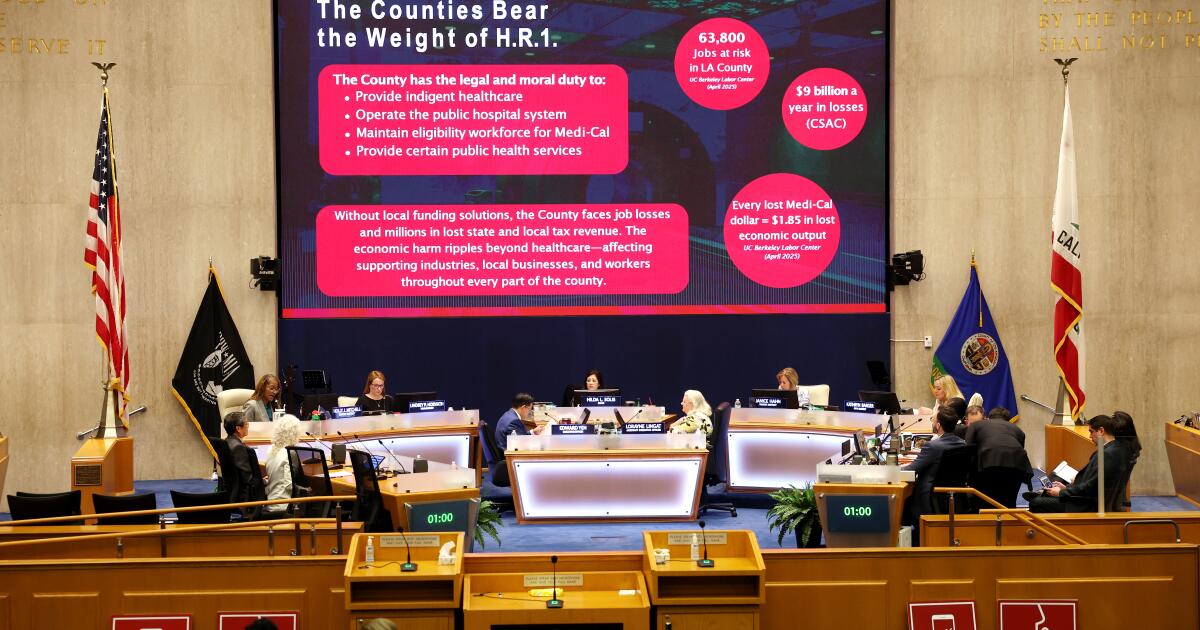
Politics2 minutes agoSupporters cheer new L.A. County healthcare sales tax: ‘It’s a lifesaver’
-

 Science7 minutes ago
Science7 minutes agoWhy new dads shouldn’t panic about low testosterone
-

 Sports14 minutes ago
Sports14 minutes agoWorld Cup referee, denied entry to U.S. because of suspected ties to terrorists, hailed in return to Somalia
-

 World22 minutes ago
World22 minutes agoUS military chief Hegseth warns Cuba against acquiring military arms
-

 News47 minutes ago
News47 minutes agoJuly 1 brings big student loan changes. Here’s what you need to know
-

 Los Angeles, Ca2 hours ago
Los Angeles, Ca2 hours agoLos Angeles High School locked down as police search for armed juvenile
-

 Detroit, MI3 hours ago
Detroit, MI3 hours ago‘Diarra From Detroit’ sets date for second season on Paramount+
-

 San Francisco, CA3 hours ago
San Francisco, CA3 hours agoSan Francisco police release video of shootout that critically wounded officer