Technology
Crooks are targeting this easy money app on your phone
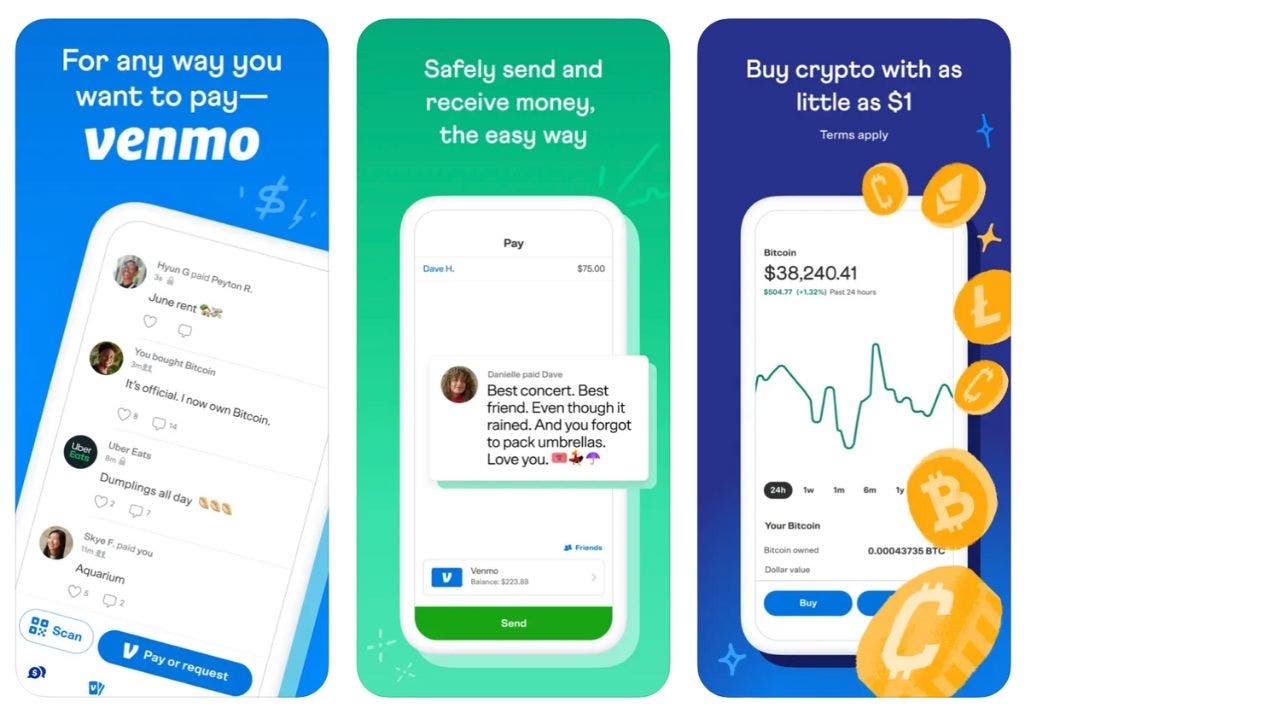
Venmo has grown in popularity, and for a good reason, because it is so easy and convenient to send and receive money electronically between you and another person.
It operates as a digital wallet linked to your bank account or debit card, which enables you to make payments quickly and easily to other Venmo users. The service is popular among younger generations as it provides a simple and social way to split bills or pay back friends for shared expenses.
Additionally, Venmo offers a social feed feature that allows you to see and comment on your friends’ transactions, adding an element of social interaction to the platform. It is available for both iPhone and Android devices.
iPhone: 4.9 stars (at time of publishing)
Android: 4.2 stars (at time of publishing)
However, with all that ease comes much targeting from scammers who want to steal your money, although unlike U.S. bank accounts, Venmo balances are not insured by the Federal Deposit Insurance Corp.
Let’s review what kind of Venmo scams to look out for and how to protect yourself.
CLICK TO GET KURT’S FREE CYBERGUY NEWSLETTER WITH SECURITY ALERTS, QUICK TIPS, TECH REVIEWS, AND EASY HOW-TO’S TO MAKE YOU SMARTER
Venmo is an app that lets you pay from a linked bank account or debit card. (CyberGuy.com)
MASSIVE FREE VPN DATA BREACH EXPOSES 360M RECORDS
Is Venmo safe to use?
Venmo uses multi-factor authentication to secure logins and encrypts all transactions to ensure the safety of your personal information. Also, you have the ability to manage your privacy and passcode settings, adding another layer of protection to your Venmo account. As a result, I would say Venmo is generally considered a safe platform to use.
However, it was designed to use with people you know and trust, such as your friends and family members, and not random people you’ve never met. When making a transaction with a person for the first time, Venmo will even ask that you enter the person’s last four digits of their phone number as an extra safety precaution.
VOICE CLONING IS THE NEW WEAPON IN SCAMMERS’ ARSENAL FOR FAMILY EMERGENCY SCHEMES
Even with these safety measures, however, people still get tricked by scams on Venmo. A common trick that scammers will use is phishing emails. A scammer will send you an email and claim to be a representative of Venmo and trick you into revealing sensitive information, such as passwords, credit card numbers, or personal details by asking you to send your personal information or click a suspicious link to “update your password” or something of that nature. These emails often mimic legitimate communications.
These kinds of scams can occur via text message or phone call as well, and unsuspecting victims may accidentally give out their banking information or even their Social Security numbers.
IS YOUR NEW ANDROID PHONE OR TV BOX ONE OF THE MILLIONS IMPACTED BY PREINSTALLED MALWARE?
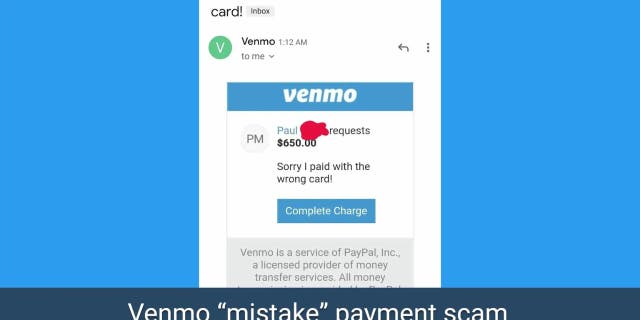
Scammers are using phishing emails to trick you into giving away your information. Here’s what to know.items (CyberGuy.com)
Scammers who are trying to sell you things online, such as on websites like Craigslist or Facebook Marketplace, will also often ask for people to pay them through Venmo. This is because Venmo’s user agreement and terms of service state that the app is meant to be used for transactions between people who know each other personally or have an established business relationship.
Scammers may ask for payment through Venmo because they know that the app lacks buyer protections and dispute resolution options. Venmo transactions are instant and irreversible, which means that if you send money to a scammer, it may be difficult or impossible to get your money back.
HOW SCAMMERS ARE SELLING COUNTERFEIT STAMPS ON FACEBOOK ADS
What types of Venmo scams should I look out for?
- Requests for personal information: Venmo will never ask you for personal or sensitive information via email, text message, or phone.
- Rental lease offers: If you’re looking for a place to rent and the landlord asks you to pay upfront via Venmo, don’t fall for it.
- Random prizes or rewards: Sometimes scammers will put up fake competitions and offer to send prize money via Venmo, but will then ask for a person’s Venmo login info to send the money. This is a common scam.
- Overpayment scams: Scammers may overpay you for an item or service and ask you to refund the difference. Once you refund the money, the scammer cancels the payment, leaving you with no money and no item or service.
THE URGENT IPHONE WARNING YOU CAN’T AFFORD TO IGNORE
How can I avoid being part of a Venmo scam?
- Look at the email address: Look closely at the address of the sender if they claim to be from Venmo. If you Google it and it’s an official email address, then it should come up right away. If it doesn’t, then it’s not really Venmo.
- Watch out for fake accounts: Scammers commonly create fake Venmo accounts claiming to be real people and will then ask family and friends of that person for money. Reach out to a person directly before sending them money.
- Public transactions: Be cautious about making your transactions public on Venmo, as scammers can use this information to target you with phishing scams or other fraudulent activities.
MALICIOUS ANDROID SPYWARE DETECTED IN OVER 100 POPULAR APPS
What to do if you believe you have been scammed on Venmo
1) The first thing you should do is contact Venmo support immediately and report the fraudulent transaction. They can provide guidance and assistance in resolving the issue.
2) Second, if you used your bank account or credit card to fund the Venmo transaction, contact your bank or credit card issuer to report the fraud and dispute the charge.
3) The third step is to change your Venmo password immediately to prevent further unauthorized transactions.
4) Also, if you believe you have been scammed, you can file a complaint with the Federal Trade Commission (FTC) to report the fraudulent activity.
5) If you feel your personal data has been stolen, and you want a service that will walk you through every step of the reporting and recovery process, one of the best things you can do to protect yourself from this type of fraud is to subscribe to an identity theft protection company.
HOW TO SHARE YOUR WHEREABOUTS IN ANY SITUATION USING YOUR CELL PHONE
This service will monitor personal information like your Home title, Social Security Number (SSN), phone number, and email address and alert you if it is being sold on the dark web or being used to open an account. They can also assist you in freezing your bank and credit card accounts to prevent further unauthorized use by criminals. One of the best parts of using some services is that they might include identity theft insurance of up to 1 million dollars to cover losses and legal fees and a white glove fraud resolution team where a U.S.-based case manager helps you recover any losses.
See my tips and best picks on how to protect yourself from identity theft by visiting CyberGuy.com/IdentityTheft.
6) Lastly, always report the scammer. If you have any information about the scammer, such as their name, phone number, or email address, report it to Venmo and the authorities.
HOW TO IDENTIFY AND STOP APPS THAT ARE LISTENING TO YOU
Kurt’s key takeaways
While Venmo is a convenient and widely used platform for electronic money transfers, you should remain vigilant against scams by being cautious of phishing emails, avoiding transactions with unknown individuals, and protecting personal information. If scammed, you should report the incident to Venmo, contact your bank or credit card issuer, change your password and file a complaint with the FTC while also providing any available information about the scammer to authorities.
Do you feel protected against the growing number of scams? What are your tools and tips? Let us know so we can alert others by writing us at Cyberguy.com/Contact.
For more of my tips, subscribe to my free CyberGuy Report Newsletter by heading to CyberGuy.com/Newsletter.
Copyright 2023 CyberGuy.com. All rights reserved.

Technology
You can buy a refurbished Steam Deck for almost half off
/cdn.vox-cdn.com/uploads/chorus_asset/file/23270010/vpavic_220210_5030_0090.jpg)
It’s not often we see an excellent portable gaming PC like the Steam Deck on sale for nearly half off, but today’s your lucky day. So long as you don’t mind buying it in certified refurbished condition, you can save hundreds when you purchase it directly (with a one-year warranty included) from Valve right now.
The refurbished Steam Deck starts at $279 for the base model with 64GB of storage, which is about $120 cheaper than buying it in new condition. And if you need more storage, the 256GB and 512GB models are both on sale, too, for $319 and $359, respectively. Given they both start at $529 and $649 in new condition, that’s almost like getting them for up to half off. What’s great, too, is that Value says it’s thoroughly tested each refurbished unit, and all meet the same performance standards as new retail units — just with some small cosmetic blemishes.
In case you need a refresher, Valve’s Steam Deck is a handheld that looks a lot like the Nintendo Switch. However, you can use it to play PC games, and it is a lot more powerful, with a seven-inch screen that’s more spacious than the one on the standard Switch. It also features tons of customizable controls, while the 512GB model even comes with an anti-glare screen.
Technology
You may not need Apple Pay to tap and pay with your EU iPhone soon
/cdn.vox-cdn.com/uploads/chorus_asset/file/23588149/IMG_0207.jpg)
Apple could soon let developers in the European Union use its tap-to-pay technology. A report from Reuters reveals that EU regulators could sign off on Apple’s proposal to open the payment system next month, putting a two-year-long legal battle to rest.
In 2022, the European Commission accused Apple of abusing “its dominant position in markets for mobile wallets.” It claimed Apple prevented third-party payment apps from using the iPhone’s NFC (near-field communication) hardware “to the benefit of its own solution,” Apple Pay.
The European Commission announced earlier this year that Apple committed to allowing third-party payment providers to freely use the iPhone’s NFC capabilities. Apple’s proposal would also give developers access to Face ID for user authentication and let iPhone users set third-party apps as their default payment option, Reuters reports.
The Commission is reportedly expected to accept Apple’s offer in May, but it has asked Apple to make some changes first. If approved, the proposal would remain in place for 10 years. We might not see these changes outside the EU, however, as Apple still hasn’t confirmed whether it will open NFC to developers located elsewhere.
Technology
Olympic organizers announce plans to use AI in sports ahead of Paris games

- Olympic organizers unveiled plans on Friday to integrate artificial intelligence into sports.
- The International Olympic Committee shared its AI plan, including identifying talent, personalizing training and improving judging fairness.
- IOC President Thomas Bach voiced the need for Olympic leadership in embracing AI responsibly.
Olympic organizers unveiled their plans Friday to use artificial intelligence in sports, joining the global rush to capitalize on the rapidly advancing technology.
The International Olympic Committee outlined its agenda for taking advantage of AI. Officials said it could be used to help identify promising athletes, personalize training methods and make the games fairer by improving judging.
“Today we are making another step to ensure the uniqueness of the Olympic Games and the relevance of sport. To do this, we have to be leaders of change,” IOC President Thomas Bach said at a press event at the former London Olympic Park, which hosted the summer games in 2012.
‘UNCONTROLLABLE’ AI SYSTEMS COULD TURN ON HUMANS, REPORT WARNS
“We are determined to exploit the vast potential of AI in a responsible way,” Bach said.
Thomas Bach, IOC President, speaks at the International Olympic Committee launch of the Olympic AI Agenda in London on April 19, 2024. Olympic organizers unveiled their plans on Friday to use artificial intelligence in sports, joining the global rush to capitalize on the rapidly advancing technology. (AP Photo/Kirsty Wigglesworth)
The IOC revealed its AI strategy as it gears up to hold the Paris Olympics, which are set to kick off in just under 100 days.
The IOC’s AI plans also include using the technology to protect athletes from online harassment and to help broadcasters improve the viewing experience for people watching from home. The IOC earns billions of dollars through the sale of broadcast rights for the games.
The local organizers of the Paris games have already sparked controversy with their plans to use artificial intelligence for security, with a video surveillance system that includes AI-powered cameras to flag potential security risks such as abandoned packages or crowd surges.
-

 News1 week ago
News1 week agoSee Maps of Where Eclipse Seekers Flocked and the Traffic That Followed
-

 Politics1 week ago
Politics1 week agoWhat to know about the Arizona Supreme Court's reinstatement of an 1864 near-total abortion ban
-

 Politics1 week ago
Politics1 week agoHouse Republicans blast 'cry wolf' conservatives who tanked FISA renewal bill
-

 News1 week ago
News1 week agoVideo: Biden Hosts Japan’s Prime Minister at the White House
-

 World1 week ago
World1 week agoRomania bans gambling in small towns
-

 Politics1 week ago
Politics1 week agoKentucky governor vetoes sweeping criminal justice bill, says it would hike incarceration costs
-

 World1 week ago
World1 week ago'Very tense' situation as floods in Russia see thousands evacuated
-

 News1 week ago
News1 week agoArizona says century-old abortion ban can be enforced; EPA limits 'forever chemicals'














